HELIOS
| This page is a work in progress and will be updated as new developments emerge. If you have information you think should be added, please create an account to enable page edits or contact a Wiki Editor. |
| Helios | |
|---|---|
| The Department of Defense has declassified access via uplink to the DSCS 3 satellite. Good Luck and Godspeed. | |
| Type | Official |
| Creator | Alice & Smith and Twitch, Inc. |
| Discovered | 2021-12-05 |
Main Page > List of Investigations > HELIOS
The Helios ARG, originally known as the DSCS III A3 ARG is an ongoing ARG produced by Alice & Smith which started on 5th December 2021. The initial trailhead informed players that access to a Department of Defense communication satellite was now authorized, with clues leading players to a stream where terminal commands led them deeper into an unknown complex.
| List of additional pages | |
|---|---|
| List of Helios terminal commands and outputs | Repository of all Helios terminal commands and their associated outputs. |
| Gallery of Helios camera checks | Repository of Helios camera check images. |
Initial Discovery
At 03:24 UTC on 2021-12-05, the Alice & Smith (A&S) Twitter account tweeted "WARNING - DSCS III A3 access has been authorized. Good Luck and Godspeed." with a link to the A&S Discord. DSCS III-A3, officially known as USA-167, is an active satellite that is part of the Defense Satellite Communications System (DSCS). The DSCS forms part of the United States' military communication network, with DSCS III-A3 specifically being the penultimate launch of this constellation in March of 2003
This was followed up at 17:05 UTC with a second tweet stating "UPDATES | Dec 5th | - DSCS III A3 IRC TOR uplink and RTMP FEED updated to version 636f-rev1.". The reference to an RTMP feed led players to a Twitch stream titled HELIOS Task Force on the dscs_iii_a3 channel.
Discovering the Stream
The stream contained an interactive terminal which users could enter commands into and get responses from. The initial terminal upon loading the stream was:
Setting hostid: 636f-rev1... Entropy harvesting: interrupt ethernet Fast boot: skipping disk checks Mounting remote file systems Starting network: DVB-TEXT DSCS-III-A3 Uplink Parameters: 7600 mhz - 7604 mhz Additional TCP/IP options: .sgov=1 Starting IRC TOR PID Manual: www.intelink.sgov.gov/wiki-ts/cmd-636f Starting background file system check in 60 seconds
Clicking on the icon to the right of the stream for the Helios terminal popped up a Twitch window describing it. This included a note saying that the command help should be used to start.
Queries and Key Systems
Converting the hexadecimal code found by inputting the version command to text produced the message command 'query' support = 1. This new command, query could be confirmed by typing in help query, which in turn has led to the discovery of the latest system inventory, chks1029 which, when queried, returned a list of currently active modules:
ERROR: chks1029 format type table 31575 | Factory Main Door 25798 | Security Terminal 75879 | Main Control Room 59579 | Nuclear Blast Door 99879 | Lights Out Factory 65548 | Assembly Line Alpha 65549 | Assembly Line Beta 65550 | Assembly Line Delta 65551 | Assembly Line Gamma 75998 | Site Alpha Invalid query for module 'chks1029'
Factory Main Door
When attempting to use the IDs from chks1029 as a part of other commands, players found that the only entry that would return anything was 31575 - the Factory Main Door. The command query 31575 informed players that there was a command to both open and close the door, however an access code was required. The command coredump 31575 provided a list of 9 individual coredump pages with various details scattered throughout.
Players quickly identified that pages 1,4 and 8 were of the same format and were likely related to the hint in the coredump 31575 command of 180 entries / GRID 20 by 9. Wth 9 blocks of data, each containing 4 lines of 5 numbers, players ended up re-arranging the numbers such that a single block would form one column of the eventual grid, with numbers transposed in order (left-to-right, top-to-bottom). e.g:
666 242 355 576 483 559
would become
666 242 355 576 483 559
By ordering the numbers in this manner, and ordering the columns according to the block numbers (1 on the left and increasing to 9 on the right), players had a complete grid that they started to investigate how to decode.
Around 00:30 UTC on 2021-12-06, those listening to the stream heard a distorted audio file play instead of the usual background track. Around 30 minutes later was discovered to have updated from showing nothing to now referencing the completion of an audio frequency render (presumed to be related to the distorted audio file slightly before).
The audio file was inspected and found to contain distinct two distinct sounds, a high pitched "sonar ping"-like sound and a deep bass sound. By looking at the number of bass sounds in a row and splitting them into groups use the high pitched sound as a delimiter, players found the numbers 2, 3, 5 and 8. These numbers correspond to the 3rd through 6th numbers in the Fibonacci sequence. While players had already been suspecting there was some sort of manipulating of filtering the large block of numbers and this file was related, it was not possible to correlate the two at the time.
At around 03:30 UTC a message was posted in chat by the DSCS_III_A3 channel which notified players that there was an "error" and "repo diff ---p3-raw-AUDIO_RENDER +++p3-clean_AUDIO_RENDER. diff files analysis IS required". In plain English, this message indicated to players that the original "raw" audio file was replaced with a new, "clean" one and that the new file will need to be analysed.
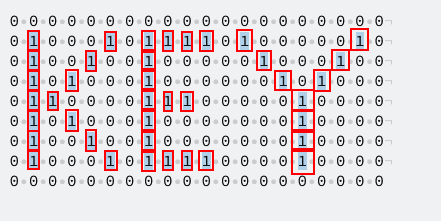
Upon listening to the file, or viewing the waveform of the audio file, players noticed that the final bass tone was removed, changing the sequence to now be 2,3,5,7. This meant it was no longer part of the Fibonacci sequence but instead they were the first 4 Prime numbers. By reviewing the 20 by 9 block of numbers and replacing all of the non-prime numbers with 0 while all of the prime numbers are changed to 1 before rotating the grid 90 degrees anti-clockwise, it was clear that the prime numbers spelled out the word key.
With this keyword, players were able to enter the command execute 31575 -open -key into the terminal. Upon entering the command players received the following confirmation:
Accessing local PGP Key /home/31337/.ssh/31575 Access authorized Requests received so far: 0 Connecting to module 31575 TAK1 - Valid TAK6 - Valid BGD8 - Valid DTB3 - Valid SDD4 - Valid Adding your entry, please wait... Process completed.
Individually there was no significant change for each single player, however as time progressed and more players entered the code, status updates were provided in chat indicating how many more entries were still needed. Initially this was 25, then 50, then 100 before finally 200. As each goal was reached, a glowing ring expanded until it encircled the door. Additionally, as goals were reached, new camera feeds were revealed and occasionally cycled through, showing other areas of the facility beyond the main door and that players would soon need to be working on.
At 11:35 UTC on 2021-12-07, the 200th command to open the door was sent and the door opened.
Security Terminal
On 2021-12-7, at 12:00 AM UTC, or 16:00 Stream Local Time, another revision was announced to the terminal program bringing it up to revision 5. This revision enabled the coredump and query commands to be used on module 25798 - Security Terminal.
On query 25798 being used in the helios terminal on the stream, its outputted two commands to be used on module 25798. The security terminal required two different inputs to be executed on it: registering a UID and committing a branchid. What these ID numbers were was not known without the information obtained when using coredump on module 25798. On using coredump 25798 5 files were generated that could be read along with the line 5 entries / 10 digits ID which seemed to indicate that a 10 digit ID number was required for this terminal. Each coredump file generated had its own clues that once investigated seemed to point towards different satellites that had been launched into space. At the time of the security terminal activating however the significance of the satellites wasn't yet clear and while several inputs were attempted based on the information of the satellites no valid entries were uncovered.
On 2021-12-8, at approximately 8:30 PM UTC, or 12:30 Stream Local Time, the terminal program had another revision bringing it up to revision 6. This brought the CSR (Clippy SubRoutine) subroutine online but is simply called clippy in the terminal commands. on using query clippy a command is listed to read various pages of its help message database where it appears to be helping an unknown individual. Amongst these pages was mention of space objects tracked by NORAD are registered with their own unique SATCAT, or Satellite Catalog, numbers. With this information the SATCAT numbers of the satellites identified with the coredump information were used as the UID number for the execute 25798 -register -<UID> command. These gave valid entries which outputted two-digit branch sequences for each of the 5 satellites. When all the branch sequences were arranged in order it produced a 10 digit code that could be inputted using the execute 25798 -commit -<branchid> command. The method of solving the UIDs and branchid are detailed below.
Page 1 Coredump Solution
On reading the page 1 coredump in the terminal three block fragments were produced that had different clues on them:
- Aug
- 134
- data.dscsiii-a3.directory/31zCVhu
The third fragment's url when put into a browser linked to an image of the Thor's Fight with the Giants painting. Combining Thor with the other infomation lead to the Thor-able expendable rocket launch system. In August this system was used to launch one satellite on vehicle 134, Explorer 6. Explorer 6's SATCAT number is 00015 which when inputted into the helios terminal using execute 25798 -register -00015 would yield the result of BranchSequence_01(a4) leading to a4 being the first digits of the branchid.
Page 2 Coredump Solution
On reading the page 2 coredump in the terminal, only one block fragment was produced with the words "Little Arrow". Little Arrow when translated into Russian yields the name Strelka, the name of one of the dogs aboard the Sputnik 5 satellite. Inputting Sputnik 5's SATCAT number, 00055, into the terminal using execute 25798 -register -00055 yields the result of BranchSequence_02(g7) leading g7 to be the next 2 digits of the branchid.
Page 3 Coredump Solution
On reading the page 3 coredump in the terminal, only one block fragment was produced with the words "92 TJ". TJ is the abbreviation for Tera Joules a method of measuring explosive yields, in particular nuclear weapons usually reach these kinds of numbers. 92 TJ can be applied to several different nuclear weapons but in keeping with the satellite theme only one really matches, China's Project 596 which was part of the Two Bombs, One Satellite project. The satellite in question was the Dong Fang Hong I or also known as China 1 which has the SATCAT number of 04382. When inputted into the terminal using execute 25798 -register -04382 it outputs the result of BranchSequence_03(x9) leading x9 to be the next two digits of the branchid.
Page 4 Coredump Solution
On reading the page 4 coredump in the terminal, two block fragments were produced that had different clues on them:
- data.dscsiii-a3.directory/3dzEo9L
- data.dscsiii-a3.directory/3y4KyIo
As with the page 1 coredump image, these URLs also link to images: Image 1 & Image 2. The first image is a logo for Interkosmos, the space program for the Soviet Union. The second image is a cropped-out piece of the School of Athens fresco which in particular is focused on Euclid. When comparing the two, no satellites launched by Interkosmos bore the name Euclid nor was Greece even involved in the program. When probing deeper with the Euclid algorithm and the countries that were part of the Interkosmos program you find there was a similar algorithm devised by an Indian astronomer called Aryabhata and which has a [https://en.wikipedia.org/wiki/Aryabhata_(satellite)/ satellite} named after that was launched in the Interkosmos program. When inputting this satellite's SATCAT number into the terminal using execute 25798 -register -07752 it yields the result of BranchSequence_04(c1) which are the next two digits of the branchid.
Page 5 Coredump Solution
On reading the page 5 coredump in the terminal, only one block fragment was produced with the number "243". Searching the number with respect to space finds that Venus has a rotational period of 243 earth days. While there is several artificial satellites in relation to Venus the one with distinction is Venera 7 which was the first one to soft-land on Venus and transmit data back to Earth. Inputting its SATCAT number into the terminal using execute 25798 -register -04489 yields the result of BranchSequence_05(d7) which are the last digits of the branchid.
25798 Solution
When all the branch sequences are arranged in order, it yields a 10 digit id number of a4g7x9c1d7 which can be inputted the terminal using execute 25798 -commit -a4g7x9c1d7 and yields the result of adding your entry to the terminal. Once 100 entries in total were collected from unique twitch ids, the hallway lights turned green and the broadcast was interrupted by a moving graphic that repeated a string of numbers and letters. Once this was over, the terminal was updated with access granted to the Main Control Room.
Main Control Room
Query & Coredump 75879
The third module began with the discovery of only two commands linked to it, being the frequently used query and coredump commands.
Entering query 75879 would return differently than the other query commands have, reading the following.
Query Module 75879 Status Request - Main Control Room Authorized commands: Unavailable Unavailable Please stand by... Module Status: Offline
Players then entered coredump 75879, returning a reference to the first module, and a list of links.
WARNING: memory coredump for 75879 Generating files... Error, Data Integrity Failed Missing reference on 31575.page7 Tracking sequence started... FOUND: data.dscsiii-a3.directory/3lL5XkY FOUND: data.dscsiii-a3.directory/3EGivlb FOUND: data.dscsiii-a3.directory/3pLvv2W FOUND: data.dscsiii-a3.directory/3EDZnEu FOUND: data.dscsiii-a3.directory/3GsEHQs FOUND: data.dscsiii-a3.directory/3IAbAMX FOUND: <error> Missing data Scan schedule: Every 4h Process Failed
The six links all redirect to twitch clips, each from seemingly normal streamers being interrupted by a similar visual & sequences of numbers as the main livestream had been.
Later the next day, two more clips were added: data.dscsiii-a3.directory/31FOELm, and data.dscsiii-a3.directory/3dyTMTY. The command also updated to say Pattern Detected: DSCS.III-A3.Authorization.XXXXXXX near the bottom, providing the format for the next solution.
| This puzzle is still being solved. New information will be added as soon as it is available. |
