Mr Robot ARG
| Mr. Robot ARG | |
|---|---|
| An ARG set in the universe of Mr. Robot | |
| Type | [[List_of_Investigations#Official|Official]] |
| Creator | NBC Universal |
| Discovered | 2017-09-28 |
Main Page > List of Investigations > Mr. Robot ARG
SPOILER WARNING: This wiki page may contain spoilers for the show Mr. Robot. The ARG is best played after catching up on the show. You have been warned!
The Mr. Robot ARG is an alternate reality game pertaining to the popular television show Mr. Robot. Throughout the course of the ARG, players interacted with characters and factions from the show, in order to solve puzzles. In particular, some players were recruited into fsociety, a fictional underground network of hackers. One of fsociety's main goals in the show is to disrupt a multinational corporation called E Corp.
Contents
San Diego Comic-Con
On the first full day of San Diego Comic-Con (July 20, 2017), attendees were exposed to promotional posters for Ecoin. These posters led players to http://e-coin.com. According to the posters and the website, Ecoin is a new cryptocurrency created by E Corp, a company in the Mr. Robot universe. By creating an account on the Ecoin website, ARG players are able to view promotional offers and enter promotional codes.
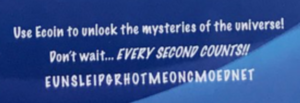
One of the Ecoin posters at SDCC had the following message:
Use Ecoin to unlock the mysteries of the universe! Don't wait - EVERY SECOND COUNTS!! EUNSLEIPGRHOTMEONCMOEDNET
By examining every second letter of the ciphertext, the following message is revealed:
USE PROMO CODE ENLIGHTENMENT
Using the promo code ENLIGHTENMENT on the Ecoin site reveals a hidden message, advising ARG players to apply for a job at Red Wheelbarrow.
More information on the SDCC event can be found in these Reddit posts: 1, 2
Ecoin Launch Event
On September 28, 2017, an invitation email was sent out to players subscribed to the mailing list. The invitation describes an Ecoin launch party, to be held on October 5. However, the email also contained a hidden message. The letters above each large bubble of champagne spelled out the message:
BITLYSEWGI
By navigating to bit.ly/sewgi, players were redirected to the RSVP page for the Ecoin launch party. At the bottom of this page, the following image was found:
The image above spells out SILENT SIN in Moon alphabet. After responding to the RSVP page with SILENT SIN, the RSVP page's appearance completely changed, and displayed the following message:
Congratulations, your eyes have been opened and we now call on you to join our resistance. On October 5th, while Evil Corp is blinded by its own opulence, we will seize control of this Ecoin bacchanal and embarrass them on a global stage. These bourgeois oppressors have fashioned themselves a golden throne and placed the legs squarely on our backs. Together, we will rise up and burn that throne to the ground. Stand with us as we fight for a new tomorrow. If, and only if, you will be attending the Ecoin Launch Party in person, leave us your email below and you will be contacted by one of our operatives with your directive soon. You must enter the same email used to RSVP to the Ecoin Launch Party. Do not share this page or this message.
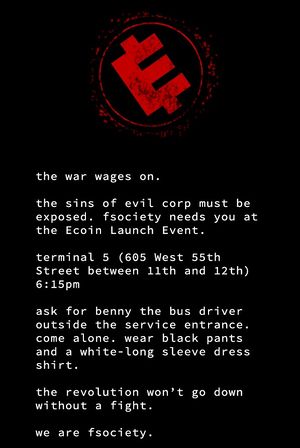
Players who entered their email addresses received the following email from fsociety, the underground network of hackers:
the war wages on. the sins of evil corp must be exposed. fsociety needs you at the Ecoin Launch Event. terminal 5 (605 West 55th Street between 11th and 12th) 6:15pm ask for benny the bus driver outside the service entrance. come alone. wear black pants and a white-long sleeve dress shirt. the revolution won't go down without a fight. we are fsociety.
October 4, 2017
On the day prior to the Ecoin launch event, several websites which were used earlier in the ARG were updated.
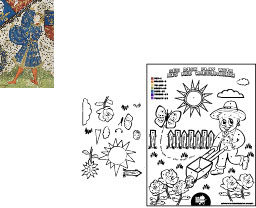
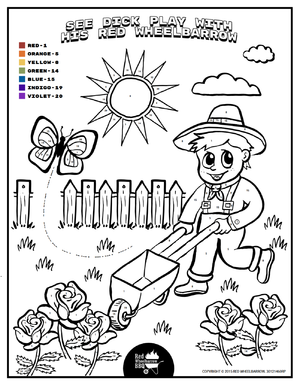
The Red Wheelbarrow site was updated with an entirely new site layout, along with a kids section. The "color by numbers" printout in the kids section contained several hidden messages.
The path traced by the butterfly is actually Morse code:
- .... . -.-- -.. --- -. - -.- -. --- .-- .-- . .- .-. . .... . .-. . -.-- . - THEY DONT KNOW WE ARE HERE YET
The numbers in the sun, when converted to letters using a simple substitution cipher, reveal the following message:
19 8 5 19 14 15 20 8 15 14 5 19 20 SHES NOT HONEST
The numbers in the butterfly's wings, when converted to letters using the same cipher, reveal the following message:
19 8 5 19 14 15 20 19 1 14 5 SHES NOT SANE
Running the file through exiftool, a thumbnail image was found.
Notable is the image in the upper left, which is a low res picture of Richard of York, shown at right. Also known as Richard Plantagenet (RP), he fought in the War of the Roses in England on the side of the White Rose, and died in battle on 30 December 1460. The date of his death and initials match the notation at the bottom of the PDF "30121460RP".
A mnemonic used to remember the colors of the rainbow, "Richard Of York Gave Battle In Vain", is also a hint in the puzzle number color key to the hidden image.
Nothing of interest has been found yet in the Spot the Difference PDF.
The Confictura site was also updated with a new quote in a hidden area, last accessed earlier in the ARG. The hidden quote can be uncovered as follows:
The visitor counter at the bottom can be adjusted manually by clicking on it. Setting the visitor counter to 0736565 causes the visitor counter to be replaced with a text box. Entering blackanddeepdesires into the text box causes the Confictura page to completely change, revealing the hidden message:
If you drink much from a bottle marked “poison” it is almost certain to disagree with you sooner or later.
This message is a quote from Lewis Carroll's Alice's Adventures in Wonderland.
(Note: the codes 0736565 and blackanddeepdesires were discovered earlier in the ARG.)
Finally, using the promo code ENLIGHTENMENT on the Ecoin site now reveals a different message than before:
to sin by silence, when we should protest, makes cowards out of men.
October 5, 2017
An hour before the event was scheduled to start, ARG players boarded the fsociety bus to the Ecoin launch party. Swag bags were distributed, some of which contained a physical Snapchat Snapcode. Scanning the Snapcode led to this URL, which plays a video automatically. Different participants received different Snapcodes, which led to different videos.
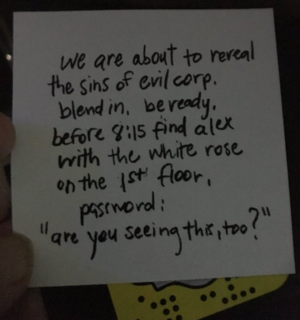
In addition to the Snapcodes, some players received handwritten notes, like the one below:
As well, some players were tweeted directives by the official Mr. Robot Twitter. These directives were targeted at ARG players who had used the hashtag WeAreFSociety. Some sample tweets are listed below:
Your eyes have been opened. Go to the champagne station and find Charles. Tell him, “I am the 99%.” Our movement can’t be stopped. Go to the serving station on Floor 2 and ask for the Chef. Tell her “I am a one, not a zero.”
At 7:30 EST, the official live stream on Mr. Robot's Facebook page went live, with 360 video providing full coverage of the event. The 360 footage was interspersed with footage of 2 interviewers, one male and one female, interviewing guests at the event. Both the interviewers and guests were actors, and provided some brief exposition about E Corp and the hacker group fsociety, as well as the fictional "Five-Nine" attacks, which spurred the development of Ecoin as a cryptocurrency.
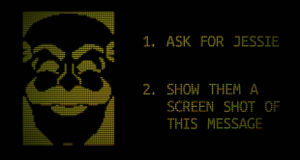
At 8:00 EST, E Corp's VP of Public Relations took the stage to welcome the attendees to the party. Shortly afterwards, the following image appeared on the livestream:
Visiting bit.ly/2yXEd2S led to a form where ARG players could fill out their mail address, along with the code MJIPQNVS (visible in the image above) to receive an FSociety mask. Shortly after, another bit.ly link and code appeared on the screen, leading to an identical site.
At 8:30 EST, a promotional video for Ecoin was played in front of the audience, and Philip Price, the CEO of E Corp, took the stage:
What a pleasure to see such an eager crowd this evening! When I look out across this room, I see faces full of hope, unbroken by circumstance... yes, we live in dark times, because our civilization, left to its own devices, will find new ways of destroying itself. Dangerous anarchists [...] have tried and failed, to undo everything we have done - everything you have worked for. But do not despair! By joining E Corp tonight, all of you show great strength and courage - and together, with the right leadership, order and stability will be restored. That is what Ecoin is all about! This new currency, this new era, is backed by one of the most powerful entities on the planet. And E Corp is here to offer a strong hand to those in need. This new currency will unite the world as one as we move into a truly digital age. I stand before you here tonight to give you this assurance, this oath: E Corp will deliver you from this chaos! Ecoin will provide a new beginning for a new world. E Corp is, and always will be, still on your side. With Ecoin, we can now move forward <whirring noise>
Price's speech was interrupted, and glitching effects began to play on the live stream, reading "HELLO FRIEND" and "CONTROL IS AN ILLUSION". At the same time, the lights in the venue went stark red, and fsociety banners were unfurled from the balconies, as some audience members put on fsociety masks. Finally, the giant capital E suspended in the air was lowered to the ground, before the video feed was cut.
Season 3, Episode 1
Season 3, Episode 1 of Mr. Robot, titled eps3.0_power-saver-mode.h, aired on October 11, 2017. The episode contained several notable ARG clues.
License Plates
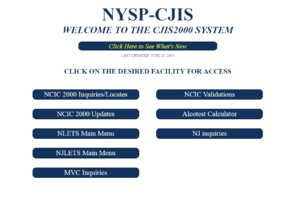
Irving, in order to call off an FBI car following him, uses an NYPD plate lookup service. The license plate of the FBI SUV is UVM7482, which he uses to find the VIN number, 1HGCM8Z633A0043F2.
Subreddits
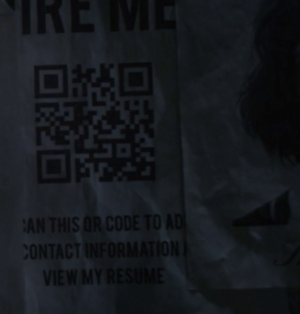
A poster with a QR code on it was discovered in the episode. Scanning this QR code led to https://jobs.runpula.net/, which was ostensibly a resume page for a Dylan C. Roberts. Prominently displayed on his resume was his experience with E Corp, which confirmed that Dylan C. Roberts was, indeed, a fictional character.
Several "Contact Me" links on Dylan's page led to the profile of Reddit user BCC4Life, who was active 2 years ago - presumably, BCC4Life is Dylan's handle online. His activity was confined to the /r/inside_e_corp subreddit, which also only displayed activity from 2 years ago. This was particularly interesting given that, at the time of discovery, the /r/inside_e_corp subreddit had only been a community for 1 month (according to its sidebar). This discrepancy was later fixed, but suggested that the Reddit adminstrators may have been involved with the ARG themselves.
At the time of discovery, several other users had posted on /r/inside_e_corp, including:
- officedrone13 (moderator of /r/inside_e_corp)
- EnnuiOtter (moderator of /r/ZenArtofAutoDetailing)
- WhatInTheActualKylie (moderator of /r/TheEclecticSlide)
- KrullFan (moderator of /r/REALMysterySpot)
Some of the NPC users from /r/inside_e_corp were found to have posted on three other fake subreddits: /r/ZenArtofAutoDetailing, /r/REALMysterySpot, and /r/TheEclecticSlide. These subreddits were similar to /r/inside_e_corp, in that all of their activity had taken place 2 years ago. All of these subreddits were private - only approved users could make submissions.
Four posts, one on each of the four subreddits, conspicuously mentioned the number 264 (1, 2, 3, 4). In these 4 posts, the following five emoticons were used: :O :d :c :x :E. When rearranged, the letters used in the emoticons spell codex, and when combined with the number 264, this clue hints at the H.264 codex, which is used in video compression. At this time, it is unclear if this puzzle holds any further significance.
Minesweeper Game
One of the episode's main plot points was hacking a minesweeper game for a "Capture the Flag" hacking challenge. After the episode aired, whoismrrobot.com, the hub site for the Mr. Robot ARG, was updated with a minesweeper.py file, which generates a Minesweeper game identical to the one described in the show. (Note: The game will not run properly on Windows, only on Linux systems.) Additionally, the game is vulnerable to a very particular exploit, the same exploit that was used in the show to hack the game and win the challenge.
More information on the Minesweeper game and its exploit can be found here.
Season 3, Episode 2
Season 3, Episode 2 of Mr. Robot, titled eps3.1_undo.gz, aired on October 18, 2017. At one point in the episode, the subreddits discovered in the previous episode were shown. Additionally, Episode 2 contained several notable ARG clues.
EC_NY Portal

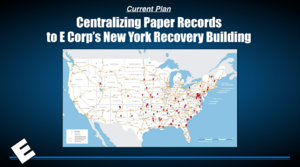
Immediately after the episode was aired, an email was sent to ARG players who had signed up for E Coin. This email encouraged players to visit whoismrrobot.com, where a new desktop portal had become available. This portal was titled EC_NY, and was, presumably, the desktop of an E-Corp machine located in New York. The desktop contained several items:
- A folder titled "HR Form Drafts" containing several drafts of a complaint against an employee, Samar Swailem
- A folder titled "Documents" containing floor plans, a map of E-Corp storage facilities, and a link to various E-Corp employee forms
- A "Nameplate Maker" app that allows a user to generate their own E-Corp nameplate
- The Employee Training video that was shown in the episode
None of these items appear to have any hidden meaning attached to them.
"Plans" Archive
At one point in the episode, a URL is visible: https://sandbox.vflsruxm.net/plans.rar. Visiting that link yielded the following text:
b3VhcUs5UjhqWHhmcEU2a0dWLnBuZwoDAuhpGqmXR9MBykrZA0BlRWMiPzYAaWtG 4y5CKWrcagjRpWw+CVQlthXGUgSkhQFSEhBGwaFVq2EkwkYSBZ6Zla40lwY0rRaF YNLMIiQT4VjFG+hgzEBJRKSWJUkjMwKs+JICQKJIEmY5LLcuW9n5fczubmbvebzu 83e/od3nd3m973dzeeec5mefmqzezsyKE+oJECBAomSmJ6C7VNf855mq/uDUU3vp 4Dq97Nz5F/BaAle0uC8p5xgnMS0+g+9yy3BrKldbq+D5tF18/XHvSipzd2CSz2qa buoI+K3HqzKb8us7zREMzox1pxL3fDuZSJ/WjIHmVg5n3GB8J49zsgrIpCs3o2Fw elehOp1zb+sPUBNrznGIbSYOKAZ9UXYnXzIr+eO7tbYlRR4HZT1ZQf4cVQpoG8PS EZMt+g1q0Oe9/0uAZ8X05JXXez3sxGm3+uFtQK6+Hto065Ku72KlNiPKTQIeyT5l crgkTqA4NF1QqPR7OXBmUrhWxcrzIaRqr/WBQXahXUrJtkXnJpgsd0wEboBRIbP4 sfItuGqV+KqWOblf5Ot64Hvy6jXyUEMgiDY51dmWVjyMKv5G5LdwZyyIJLKbIri1 C6Te+w/dZRNa+LP+Nt0x/ZZdyAlVWR3jJ/scC6msO/Q+4WmJ7n6Kzk80AobYK4pI DOwx2Uei8FCZS/JFYrCthCdW4T4VpcoPaJZY3lI7Rfx6qhjsmRWpLoFK0b7aLR9l YfKROnNI885Mp2ywOKkoSxboKOJlVp7WVGwTsTQcNxc7vKbP/yEEPbVJRb8ZdbtE PVMYEWp6/CnHuhT7N1CWQP+lLHLU3LKw5+NWfyakyxF4hXHJAHMZc2t0UdKNrA8m p7FsXvA/shbhioeagOCmZTIkFWPjXHwylCrUYlP8AOPrfEJur1n4og/+/HL/c6Y5 pksv3JtvDwlx6u78GsXPu7kmlFPzO1sO/p9Lt0FKp9MgDSZdvauPtO9lWFIJfHp7 /8N08CseGojeBhTMJQokVvyljS7QLP20EevozBIfJAZ+C7fFYeeaDvOmkqvrU0ip jgIWnUv/IJbAhKH3Cr+jg5aUhW4UTHd3Q0wdnNq4afNttSRwaJuX7MGjFTdewGM9 LbYN/wIRSwib3+M2mGuywZ92YVVFpjZ4vMhNMSw9eLUFaMhfDXMnUe2M51XusaVF qiQCyf63UDCPCQ8P0bfElu/UvS2+NyX0ALh+pSx9dxrjn3tmO9htRYwHwu5ebeXR ZD6p9CyMpd4is9eDfl9+IspNGtGMaOntIJiBc8RzmvR4oOxlK3jP9ZJ4Rc+Qu4hx k+O/EeVJkZ2Y6hDg/OAdd1ZRAwUEAA==
This data is encoded in Base64, and can be decoded (eg. with this site). By opening the decoded file as a RAR file, its contents could be extracted. The RAR archive contained an image of a QR code, which, when scanned, led here. This page contains a real-world exploit that was used by the FBI in this episode of Mr. Robot, to view a target's monitor. Because this page is publicly accessible, it is thought to be the conclusion of this particular puzzle trail.
E-Corp Webmail
Another link was shown in the episode at one point: https://webmail.e-corp-usa.com/owa/. Visiting this website yields a login prompt. In the episode, two characters' login credentials were shown:
[email protected] / aboynamedg00 peter.mccleery / tapitback!
Using each of these login credentials yielded the following 2 error messages:
INCORRECT FIELD INPUT. ERROR #13489-RARECHPOT INCORRECT FIELD INPUT. ERROR #123578-PARMLETOR
Both error numbers contain a series of digits followed by a series of letters. By taking the letters in the positions of the digits, two distinct anagrams were discovered:
RARECHPOT 1 34 89 R RE OT Anagram: RETRO PARMLETOR 123 5 78 PAR L TO Anagram: PORTAL
Logging into the website with the username RETRO and the password PORTAL links to a PDF file containing a presentation that was seen in the show.
E-Corp Badge
At one point in the episode, a QR code is shown on Elliot's E-Corp employee badge. Scanning the QR code leads to this URL: http://www.e-corp-usa.com/company_directory/elliot_alderson/
No puzzles have been found on this webpage.
E-Corp Shipping
A link was shown in the episode at one point: http://www.e-corp-usa.com/cp/directory/shipping/1088989/. Visiting this website yields a login prompt - the correct login credentials have yet to be determined.
Season 3, Episode 3
Season 3, Episode 3 of Mr. Robot, titled eps3.2_legacy.so, aired on October 25, 2017.
Babycam IP
At one point in the episode, the following IP address was shown: 192.251.68.238, which links to https://y9bukwer.bxjyb2jvda.net/. This website is ostensibly a webcam monitoring site, which was used in the show to watch an infant. Instead of a video feed, the webpage randomly selects an image of static, which is a GIF file.
In the last frame of the static, a hidden message can be seen:
Cleaned up:
68 65 72 65
This is hexadecimal for the word here. At this time, the significance of the word is unclear. Each of the other static animations have hidden messages as well - so far, a message has been discovered in each:
| Link | Ciphertext | Plaintext |
|---|---|---|
| 1 | 77 65 26 23 33 39 3b 72 65
|
we're
|
| 2 | 61 6c 6c
|
all
|
| 3 | 6d 61 64
|
mad
|
| 4 | 68 65 72 65
|
here
|
Together, these 4 words form the sentence we're all mad here, a reference to Lewis Carroll's Alice in Wonderland.
rvzjtenpula.net
At one point in the episode, the domain name https://www.rvzjtenpula.net/ is visible. The only thing on that page is an innocuous 403 error - if it has further meaning, it has yet to be determined.
Season 3, Episode 4
Season 3, Episode 3 of Mr. Robot, titled eps3.3_metadata.par2, is scheduled to air on November 1, 2017.