Difference between revisions of "Sombra ARG"
(Major reformat.) |
(Rejected the last text change (by Itechbrand) and restored revision 19078 by 01101000 01101001) |
||
| (17 intermediate revisions by 7 users not shown) | |||
| Line 11: | Line 11: | ||
}} | }} | ||
| − | {{ArgHeader | + | {{ArgHeader}} |
| + | |||
The Sombra ARG was an ARG for the first-person shooter [https://www.playoverwatch.com Overwatch], developed by [https://www.blizzard.com/ Blizzard Entertainment]. Sombra was the name of a then-unreleased Overwatch hero. The ARG was comprised of clues and ciphers referencing Sombra, which were found in various developer updates and short animations. | The Sombra ARG was an ARG for the first-person shooter [https://www.playoverwatch.com Overwatch], developed by [https://www.blizzard.com/ Blizzard Entertainment]. Sombra was the name of a then-unreleased Overwatch hero. The ARG was comprised of clues and ciphers referencing Sombra, which were found in various developer updates and short animations. | ||
| Line 176: | Line 177: | ||
[[File:achievements.png|thumbnail|right|"¿" Achievement, comment in source code]] | [[File:achievements.png|thumbnail|right|"¿" Achievement, comment in source code]] | ||
| − | The phrase "you need to analyze your previous achievements" led players to look at the achievements on the [https://www.playoverwatch.com Overwatch] website. It was | + | The phrase "you need to analyze your previous achievements" led players to look at the achievements on the [https://www.playoverwatch.com Overwatch] website. It was noticed that by logging in and viewing the achievements on a player profile, a mystery achievement appeared. Examining a hex dump of the image lead players to a new phrase: |
<pre> | <pre> | ||
| Line 247: | Line 248: | ||
== Overwatch Forums Glitching Page/ "Skycoder" == | == Overwatch Forums Glitching Page/ "Skycoder" == | ||
| − | + | On August 23rd, 2016, at an unknown time, an [https://us.battle.net/forums/en/overwatch/topic/20748794686 ominous post] by a user named "Skycoder" appeared on the official General Discussion forums for Overwatch. | |
| − | + | Players found that the name of the post, <code>00110010 00110011</code>, was binary for "23," which was a direct reference to Sombra being the 23rd hero in Overwatch. The age of the post started at 24 hours, and counted down rather than increasing. The post itself contained a single sentence in Spanish: | |
| − | + | <pre> | |
| − | + | la que tiene la información; tiene el poder | |
| − | + | </pre> | |
| − | + | Which, when translated to english, reads: | |
| − | + | <pre> | |
| + | She who has the information, has the power. | ||
| + | </pre> | ||
| − | and | + | After a short while, the post glitched and distorted, gradually turning a hue of purple. A text box then appeared, which printed the following ciphertext: |
<pre> | <pre> | ||
| Line 295: | Line 298: | ||
=== ASCII Skull #2 === | === ASCII Skull #2 === | ||
| − | + | Players discovered that this was Base64 and, once decrypted, resulted in another ASCII skull: | |
| + | <pre> | ||
:PB.Bk: | :PB.Bk: | ||
,jBˆ@B@B@B@BBL. | ,jBˆ@B@B@B@BBL. | ||
| Line 322: | Line 326: | ||
vMB :@B@ :BO7 | vMB :@B@ :BO7 | ||
,B@B | ,B@B | ||
| + | </pre> | ||
| − | + | Players discovered that, once both skulls had been stripped of spaces, the bytes of each skull that aren't equal to 0 could be subtracted using [https://pastebin.com/g3kA1Pif a script]. Once compiled, players received the following string: | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| + | <pre> | ||
OHVSURPHWLXQMXHJR...FUHRTXHXVWHGHVORVGHWHFWLYHVGHMXHJRVOROODPDULDQXQWUDLOKHDG?EOCJGDXVD-DPEDV-FDODYHUDV.KWPO | OHVSURPHWLXQMXHJR...FUHRTXHXVWHGHVORVGHWHFWLYHVGHMXHJRVOROODPDULDQXQWUDLOKHDG?EOCJGDXVD-DPEDV-FDODYHUDV.KWPO | ||
| + | </pre> | ||
| − | + | Players discovered that this was a caesar cipher. After shifting the string forward 23 places, it resulted in: | |
| + | <pre> | ||
LESPROMETIUNJUEGO...CREOQUEUSTEDESLOSDETECTIVESDEJUEGOSLOLLAMARIANUNTRAILHEAD?BLZGDAUSA-AMBAS-CALAVERAS.HTML | LESPROMETIUNJUEGO...CREOQUEUSTEDESLOSDETECTIVESDEJUEGOSLOLLAMARIANUNTRAILHEAD?BLZGDAUSA-AMBAS-CALAVERAS.HTML | ||
| + | </pre> | ||
| − | When cleaned up | + | When cleaned up, the message read: |
| + | <pre> | ||
Les prometi un juego...creo que ustedes los Detectives de Juegos lo llamarían un trailhead? BLZGDUSA-AMBAS-CALAVERAS.HTML | Les prometi un juego...creo que ustedes los Detectives de Juegos lo llamarían un trailhead? BLZGDUSA-AMBAS-CALAVERAS.HTML | ||
| + | </pre> | ||
When translated from Spanish to English: | When translated from Spanish to English: | ||
| + | <pre> | ||
I promised you a game...I believe you Game Detectives would call it a trailhead? BLZGDAUSA-AMBAS-CALAVERAS.HTML | I promised you a game...I believe you Game Detectives would call it a trailhead? BLZGDAUSA-AMBAS-CALAVERAS.HTML | ||
| + | </pre> | ||
| − | + | <code>USA-AMBAS-CALAVERAS</code> translated to <code>USE-BOTH-SKULLS</code>, and the <code>.HTML</code> extension hinted at a URL. | |
=== Skull Video === | === Skull Video === | ||
| − | BLZGDA | + | BLZGDA refers to the servers that Blizzard uses to host media on their website. As such, this led players to [ https://blzgdapipro-a.akamaihd.net/media/screenshot/usa-ambas-calaveras.html this page], which contains a video of a vitals screen depicting a skull and some other medical information. In addition, it also contained a graphic of one of the ASCII skulls. An Imgur mirror can be found [https://i.imgur.com/6Pk69LX.png here]. |
| − | + | ||
| + | Within the properties of the video, players found another comment in Spanish: | ||
| − | + | <pre> | |
| + | Parecen estar muy interesados en estos "héroes". ¿Tal vez les interese conocer algunos detallitos que he averiguado sobre ellos? | ||
| + | </pre> | ||
| − | + | In English: | |
| − | + | <pre> | |
| − | |||
You seem to be very interested in these "heroes". Maybe interested to know some details that I found out about them? | You seem to be very interested in these "heroes". Maybe interested to know some details that I found out about them? | ||
| + | </pre> | ||
| − | + | In addition, the video contains a heartbeat monitor, and a series of 26 lines above it. When players assigned the letters of the alphabet to the 26 lines, and used the "pings" of the heartbeat to determine what letters to use, the following string was found: | |
| + | <pre> | ||
momentincrime | momentincrime | ||
| + | </pre> | ||
=== amomentincrime E-mail === | === amomentincrime E-mail === | ||
| − | 'momentincrime' appeared to refer to the Roadhog and Junkrat | + | 'momentincrime' appeared to refer to the in-universe TV show "A Moment in Crime," which can be seen in the Roadhog and Junkrat [https://www.youtube.com/watch?v=l5kTATxt7bE video] that came out months before the release of Overwatch. However, players also discovered a website, [https://amomentincrime.com amomentincrime.com], and displayed the following text: |
| + | <pre> | ||
...Estableciendo conexión... | ...Estableciendo conexión... | ||
...Protocolo Sombra v1.3 iniciado... | ...Protocolo Sombra v1.3 iniciado... | ||
| Line 374: | Line 387: | ||
...Terminando conexión... | ...Terminando conexión... | ||
| + | </pre> | ||
| − | + | Players discovered that sending an e-mail to [email protected] resulted in an automated email response: | |
<pre> | <pre> | ||
| Line 401: | Line 415: | ||
</pre> | </pre> | ||
| − | + | Players discovered that, if the sets of numbers were taken as AA:BB:CC, where AA was the number of skull (in order of discovery), BB was the row and CC was the column (as seen [https://i.imgur.com/ZgN2MVQ.png here]), and organized into a 5x5 matrix, it would result in: | |
<pre> | <pre> | ||
| Line 411: | Line 425: | ||
</pre> | </pre> | ||
| − | + | Players discovered that this Matrix could be used as a bifid key to decode the text underneath the table of numbers in the email, as shown below: | |
| − | + | <pre> | |
j . 7 F 5 7 O , N L v : q j . 7 B : , 1 q v @ B 1 j 5 i v B : , | j . 7 F 5 7 O , N L v : q j . 7 B : , 1 q v @ B 1 j 5 i v B : , | ||
12 21 42 54 53 42 24 32 45 15 33 34 44 12 21 42 14 34 32 55 44 33 22 14 55 12 53 31 33 14 34 32 | 12 21 42 54 53 42 24 32 45 15 33 34 44 12 21 42 14 34 32 55 44 33 22 14 55 12 53 31 33 14 34 32 | ||
| Line 420: | Line 434: | ||
11 24 23 14 43 22 55 45 54 34 43 23 22 42 31 24 45 55 11 52 35 33 33 41 43 43 11 24 23 14 43 22 | 11 24 23 14 43 22 55 45 54 34 43 23 22 42 31 24 45 55 11 52 35 33 33 41 43 43 11 24 23 14 43 22 | ||
| + | </pre> | ||
| + | |||
| + | This gave players the following string: | ||
SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@ | SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@ | ||
| + | This phrase was found to be leet-speak, and was translated to: | ||
| − | + | <pre> | |
| − | |||
Sombra Information is power Sombra | Sombra Information is power Sombra | ||
| + | </pre> | ||
| − | The string <code>SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@</code> was used as a password later on in the ARG. | + | The string <code>SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@</code> was used as a password later on in the ARG. |
== A Moment in Crime Transmission == | == A Moment in Crime Transmission == | ||
| Line 435: | Line 453: | ||
Once the 23-hour countdown on the Skycoder forum post reached zero, [https://amomentincrime.com amomentincrime.com] was updated. It now read: | Once the 23-hour countdown on the Skycoder forum post reached zero, [https://amomentincrime.com amomentincrime.com] was updated. It now read: | ||
| + | <pre> | ||
...Estableciendo conexión... | ...Estableciendo conexión... | ||
...Protocolo Sombra v1.9 iniciado... | ...Protocolo Sombra v1.9 iniciado... | ||
| Line 441: | Line 460: | ||
...Terminando conexión... | ...Terminando conexión... | ||
| + | </pre> | ||
| − | + | Translated from Spanish to English: | |
| + | <pre> | ||
...Establishing connection... | ...Establishing connection... | ||
...Sombra Protocol v1.9 initiated... | ...Sombra Protocol v1.9 initiated... | ||
| − | |||
...Transmitting information to active omnics... 2% | ...Transmitting information to active omnics... 2% | ||
...Ending connection... | ...Ending connection... | ||
| + | </pre> | ||
| − | A comment was added | + | A comment was also added to the source code: |
| + | |||
| + | <pre> | ||
Bien hecho, ya tienen mi clave. Hackear este programa de televisión no tuvo chiste. Espérense a lo que sigue. | Bien hecho, ya tienen mi clave. Hackear este programa de televisión no tuvo chiste. Espérense a lo que sigue. | ||
| + | </pre> | ||
| + | |||
| + | When translated: | ||
| + | |||
| + | <pre> | ||
Well done, you have my password. Hacking this television program was meaningless. Wait for what is coming. | Well done, you have my password. Hacking this television program was meaningless. Wait for what is coming. | ||
| + | </pre> | ||
| + | |||
| + | The percent on the amomentincrime.com slowly increased over time. Once the 5% milestone was hit, the Sombra Protocol version number changed to to v1.95. Afterwards, the percentage increased by 0.0038% every 3 minutes in real time. | ||
| − | + | In addition, another comment was added: | |
| − | + | <pre> | |
Parece que se están calentando un poco las cosas... tendré que pasar desapercibida mientras esto se finaliza. | Parece que se están calentando un poco las cosas... tendré que pasar desapercibida mientras esto se finaliza. | ||
| + | </pre> | ||
| + | |||
| + | Translated: | ||
| + | |||
| + | <pre> | ||
It seems things are heating up a bit... I'll have to go unnoticed while this is finishing. | It seems things are heating up a bit... I'll have to go unnoticed while this is finishing. | ||
| + | </pre> | ||
| − | On 18th October at 19:02 GMT the site reached 100%, and the site updated | + | On 18th October at 19:02 GMT the site reached 100%, and the site updated with the following message: |
| + | <pre> | ||
...Transmisión finalizada - finalizando carga... | ...Transmisión finalizada - finalizando carga... | ||
...Carga finalizada. Unidad Bastion E-54 comprometida... | ...Carga finalizada. Unidad Bastion E-54 comprometida... | ||
| + | </pre> | ||
Which roughly translates to: | Which roughly translates to: | ||
| + | <pre> | ||
...Transmission complete - finishing upload... | ...Transmission complete - finishing upload... | ||
...Upload finished. Unit Bastion E-54 engaged... | ...Upload finished. Unit Bastion E-54 engaged... | ||
| + | </pre> | ||
| − | Hidden in the source code of the site was | + | Hidden in the source code of the site was the text <code>v1.4.0.2.324??</code>. Players then correctly assumed that this referred to a future build of Overwatch itself. |
| − | |||
| − | |||
| − | |||
| − | |||
== Sombra vs. LumériCo == | == Sombra vs. LumériCo == | ||
| Line 481: | Line 518: | ||
=== The Hacked Bastion === | === The Hacked Bastion === | ||
| − | On 2016 | + | On October 19, 2016, a new Overwatch version was released - version 1.4.0.2.32448. Shortly afterwards, the version number in the source code of the amomentincrime site updated to the same version number. After the build launched, players discovered that the hero Bastion had a strange interaction when near the "SOMBRA PROTOCOL" monitors on Dorado, and would emit a message in morse code, which can be heard [https://www.youtube.com/watch?v=Hkd__ceYm-Y here]. When the morse was decoded, players received the following string: |
| − | |||
| − | |||
| − | |||
<pre> | <pre> | ||
SQOFJFBNITIZWGDXSDO | SQOFJFBNITIZWGDXSDO | ||
</pre> | </pre> | ||
| − | + | Players discovered that this was a Vigenere cipher, and the key consisted of the alphabetic characters from the | |
| + | <code>SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@</code> string, it was decoded to read: | ||
<pre> | <pre> | ||
| Line 495: | Line 530: | ||
</pre> | </pre> | ||
| − | This led to the | + | This led players to the [https://lumerico.mx/ LumeriCo website]. ''(Editor's note: as of 2018, this site appears to be inactive.)'' |
=== LuméReaction === | === LuméReaction === | ||
| Line 501: | Line 536: | ||
[[File:Lumerico.png|thumbnail|right|The homepage of https://lumerico.mx]] | [[File:Lumerico.png|thumbnail|right|The homepage of https://lumerico.mx]] | ||
| − | The LumeriCo website was for | + | The LumeriCo website was for the in-universe Mexican tech giant LumériCo, who had built several reactors in the Dorado region. The website had a [https://lumerico.mx/news news page], noting the imminent opening of a new reactor on November 1 as well as a recent attack on its construction site. There were also [https://lumerico.mx/about About] and [https://lumerico.mx/login Login] pages. |
| − | + | Players also discovered a <code>robot.txt</code> file, which appeared to server no purpose and only contained the text <code>Allow: omnics</code>, and appeared to be a joke about the [https://en.wikipedia.org/wiki/Robots_exclusion_standard Robots exclusion standard]. Another text file was discovered called <code>omnics.txt</code>, which contained the text: | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| + | <pre> | ||
Allow: ?? | Allow: ?? | ||
Allow: ??? | Allow: ??? | ||
| + | </pre> | ||
| − | + | And appeared to be yet anotehr joke about the Robots exclusion standard. And, finally, an <code>api</code> file that contained <code>{"message":"thanks for calling the api"}</code> and, humorously, has no practical purpose. | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
=== Phone Number === | === Phone Number === | ||
| − | At the bottom of the | + | At the bottom of the LumeriCo website, players discovered a phone number <code>(510) 766-2726</code>. When called, players heard a woman listing off a string of numbers in Spanish, a recording of which can be found [https://soundcloud.com/jackwilsdon/510-766-2726a here]. The numbers spoken are: <code>5-2-4-1-3 (pause) 23-4-14-8-6-18-17-23-21-18-15</code>. |
| − | + | When assuming that a=1, b=2, etc, the second part of the message can be decoded to: <code>WDNHFRQWURO</code>. This was found to be a ROT-23 cipher, and decoded to: <code>TAKECONTROL</code>. | |
| − | |||
=== Take Control === | === Take Control === | ||
| − | The phone message | + | The phone message led players to an important [https://lumerico.mx/TAKECONTROL/index.html page] on the site, under the directory <code>TAKECONTROL</code>. It was styled the same way as amomentincrime.com and featured [https://lumerico.mx/calavera.png an image of Sombra's skull icon], named "calavera.png". There was also text on the page: |
<pre style="word-break:break-all;word-wrap: break-word;"> | <pre style="word-break:break-all;word-wrap: break-word;"> | ||
| Line 544: | Line 566: | ||
</pre> | </pre> | ||
| − | + | Players found this to be a column order transposition cipher with the key <code>5 2 4 1 3</code>, which was found in the phone message. The cleaned up result was: | |
| + | <pre> | ||
Los felicito por haber llegado hasta aquí. Solo quería saber si estaban listos. (Hey, es muy difícil encontrar buena ayuda últimamente...deberían ver algunos de los payasitos que están trabajando conmigo) Por ahora, continuemos con el verdadero reto: acabar con LumériCo y su president e Guillermo Portero. ¿Y porqué? Porque es un hombre codicioso, corrupto y un ladrón abominable. Su plan de traer en línea el más grande y el más poderoso zigurat el 1 de noviembre no es nada más que una artimaña, un elaborado plan designado para ejercer aún más influencia sobre la gente de México y en gordar los bolsillos de sus compinches. ¿Y quién va a pagar por eso? La gente común y corriente, los mismos que siempre quedan olvidados. | Los felicito por haber llegado hasta aquí. Solo quería saber si estaban listos. (Hey, es muy difícil encontrar buena ayuda últimamente...deberían ver algunos de los payasitos que están trabajando conmigo) Por ahora, continuemos con el verdadero reto: acabar con LumériCo y su president e Guillermo Portero. ¿Y porqué? Porque es un hombre codicioso, corrupto y un ladrón abominable. Su plan de traer en línea el más grande y el más poderoso zigurat el 1 de noviembre no es nada más que una artimaña, un elaborado plan designado para ejercer aún más influencia sobre la gente de México y en gordar los bolsillos de sus compinches. ¿Y quién va a pagar por eso? La gente común y corriente, los mismos que siempre quedan olvidados. | ||
| Line 553: | Line 576: | ||
GFlores/g#fNwP5qJ | GFlores/g#fNwP5qJ | ||
| + | </pre> | ||
Translated: | Translated: | ||
| + | <pre> | ||
I'm congratulating you for getting in here. I only wanted to know if you were ready or not. (Hey, it's really difficult to get good help lately... you should see some of the clowns I'm working with). For now, let's continue with the true challenge: taking down Lumerico Corp president Guillermo Portero. Why? Because he's a greedy and corrupt man, and an abominable thief. His plan of bringing in line the most powerful and biggest zigurat the 1st of november us nothing more than a deceit, an elaborate plan by his gang to become even more influential in the people of Mexico and get more money. And who's gonna pay for that? Common people, the ones that are always forgotten. | I'm congratulating you for getting in here. I only wanted to know if you were ready or not. (Hey, it's really difficult to get good help lately... you should see some of the clowns I'm working with). For now, let's continue with the true challenge: taking down Lumerico Corp president Guillermo Portero. Why? Because he's a greedy and corrupt man, and an abominable thief. His plan of bringing in line the most powerful and biggest zigurat the 1st of november us nothing more than a deceit, an elaborate plan by his gang to become even more influential in the people of Mexico and get more money. And who's gonna pay for that? Common people, the ones that are always forgotten. | ||
| Line 563: | Line 588: | ||
GFlores/g#fNwP5qJ | GFlores/g#fNwP5qJ | ||
| + | </pre> | ||
=== Presidential Login === | === Presidential Login === | ||
| − | + | Players used the credentials above on the [https://lumerico.mx/login Lumerico login page], and accessed the account of Gonzalo Flores, which included [https://lumerico.mx/email his emails]. Transcripts of these emails were archived [https://docs.google.com/spreadsheets/d/1zh7OU2dEOnD4X43ImvZBNpS75FLkj-rL75pXJ2l3TuQ/htmlview?sle=true# here]. | |
| − | + | However, only one email had relevance to the ARG: | |
<pre> | <pre> | ||
| Line 582: | Line 608: | ||
</pre> | </pre> | ||
| − | The email | + | The email referenced high traffic on the [https://lumerico.mx/president-bypass President Bypass Link]. The page displayed an "access denied" message, but players found a <code>President Auth-Bypass Revision 1.02: /.git/</code> line in the source code. |
| − | This line led players to [https://github.com/internetwache/GitTools/tree/master/Dumper dump the data] from the [https://lumerico.mx/president-bypass/.git/ /.git/ subpage] with git protocol and upload it to [https://gist.github.com/anonymous/987beb6a5c817b53da820562854bdebe Github]. | + | This line led players to [https://github.com/internetwache/GitTools/tree/master/Dumper dump the data] from the [https://lumerico.mx/president-bypass/.git/ /.git/ subpage] with git protocol and upload it to [https://gist.github.com/anonymous/987beb6a5c817b53da820562854bdebe Github]. These were the code files behind the website, and included a '''class.authentication.php''' file that contained an encryption function, and '''class.president-bypass.php''' file which contained the president's (Guillermo Portero) username, <code>GPortero</code>, and encrypted password <code>?MzY:MTI5:?AzY:OWM?:?EDO:ZGU?:jVTM:MTJm:2ITM:MTUw:?QjY:OWY?:?kTO:MTQx:?MzY</code>. |
| − | + | Some players wrote a function to decode the encrypted <code>class.authentication.php</code> file, and then used it on the encrypted password. The resulting password was <code>Xy@4+Bkuqd<53uJ</code>. | |
After logging in to the President's account, players were able to read his emails. After 30 minutes, another email appeared in the President's inbox, from Sombra herself: | After logging in to the President's account, players were able to read his emails. After 30 minutes, another email appeared in the President's inbox, from Sombra herself: | ||
| Line 597: | Line 623: | ||
</pre> | </pre> | ||
| − | The rough translation | + | The rough translation was: |
<pre> | <pre> | ||
| Line 609: | Line 635: | ||
[[File:Lumerico admin panel.png|thumbnail|right|The admin panel of the Lumerico site, only accessible by logging in as MJimenez]] | [[File:Lumerico admin panel.png|thumbnail|right|The admin panel of the Lumerico site, only accessible by logging in as MJimenez]] | ||
| − | On October 25, new emails were discovered in the GFlores account, but they had no immediate significance to the ARG. In addition, omnics.txt was updated: | + | On October 25, 2016, new emails were discovered in the GFlores account, but they had no immediate significance to the ARG. In addition, omnics.txt was updated: |
<pre> | <pre> | ||
| Line 616: | Line 642: | ||
</pre> | </pre> | ||
| − | Tzolk'in is the name of a [[Wikipedia:Maya calendar#Tzolk'in|Mayan Calendar]], and the second line was a series of animals from it in the Tzolk'in dialect. Imix stands for Day 1, Chikchan — 5, Manik — 7 and Kimi — 6. | + | Tzolk'in is the name of a [[Wikipedia:Maya calendar#Tzolk'in|Mayan Calendar]], and the second line was a series of animals from it in the Tzolk'in dialect. Imix stands for Day 1, Chikchan — 5, Manik — 7 and Kimi — 6. When turned into numbers, the string read <code>1 57 1 5151 7 5 1 6 5 5 6 5151 56</code>. These digits turned into pictograms of [[Wikipedia:Maya numerals|Maya numerals]] (one by one, not numbers as a whole) written horizontally become <code>. -..- . -.-. ..- - . .- - - .- -.-. -.-</code> This was found to be morse code, and decoded to: <code>EXECUTEATTACK</code>. |
| − | This led | + | This led players to the "EXECUTEATTACK" [https://lumerico.mx/EXECUTEATTACK/index.html directory], where the following text was discovered: |
<pre> | <pre> | ||
| Line 632: | Line 658: | ||
</pre> | </pre> | ||
| − | Logging in with the credentials <code>MJimenez / d0r*NuLw9</code> gave | + | Logging in with the credentials <code>MJimenez / d0r*NuLw9</code> gave players access to the [https://lumerico.mx/admin admin panel] of the LumeriCo reactor. Until November 1, 2016, it stayed inactive and any command was answered with the same message saying that the terminal disconnected. |
=== The Terminal === | === The Terminal === | ||
Once the console became usable, players could type <code>help</code> to see a list of commands: | Once the console became usable, players could type <code>help</code> to see a list of commands: | ||
| − | + | <pre> | |
| − | + | override Engineer safety mode override | |
| − | + | help Provides help information about commands | |
| − | + | version Displays system version information | |
| − | + | about Displays information about the system | |
| + | grep Search output by string | ||
| + | </pre> | ||
| − | In the MJimenez email account, there was an email labeled <code>Corrupción de correo electrónico</code> with highlighted text in side of it, specifically <code>/ter/</code>. | + | In the MJimenez email account, there was an email labeled <code>Corrupción de correo electrónico</code> with highlighted text in side of it, specifically <code>/ter/</code>. Players discovered that performing the Linux command <code>about | grep 'ter'</code> in the console returned this text: |
| − | + | <pre> | |
| − | + | Open source lightweight shell for any terminal. | |
| − | + | Anything with a terminal | |
| + | 1.1.0 - expanded terminal support | ||
| + | </pre> | ||
| − | The first word of every line given from the output was | + | The first word of every line given from the output was bolded and purple. Putting the letters together, players received the text <code>OpenAnything1.1.0</code>, which was a later solution. |
| − | Another available command for the terminal was | + | Another available command for the terminal was <code>override</code>, and prompted players with three security questions: |
# '''Favorite Movie'''. The answer to the prompt is <code>some like it bot</code>, a movie from the Overwatch universe. | # '''Favorite Movie'''. The answer to the prompt is <code>some like it bot</code>, a movie from the Overwatch universe. | ||
| Line 663: | Line 693: | ||
'''exec''' Execute a file | '''exec''' Execute a file | ||
| − | Typing <code>ls</code> listed two files: <code>payload</code> and <code>d_ilqh_nhb.html</code> (the file name | + | Typing <code>ls</code> listed two files: <code>payload</code> and <code>d_ilqh_nhb.html</code> (the file name was a ROT23 for ''a_fine_key''). |
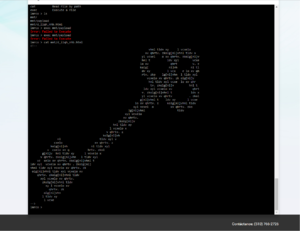
| − | [[Image:A fine key.png|thumb|right|a_fine_key.html]] Reading the second file with <code>cat mnt/d_ilqh_nhb.html</code> yielded a text where ASCII characters (repeating string <code>vhnl tldv xyl vcxelo xv qhrtv. zkolg[nl]</code>) were in a shape of a key. Deciphering it using | + | [[Image:A fine key.png|thumb|right|a_fine_key.html]] Reading the second file with <code>cat mnt/d_ilqh_nhb.html</code> yielded a text where ASCII characters (repeating string <code>vhnl tldv xyl vcxelo xv qhrtv. zkolg[nl]</code>) were in a shape of a key. Deciphering it using an Affine cipher (A=23, B=23) yielded the following string: <code>some keys are shaped as locks. index[me]</code>. It is assumed that ''some keys are shaped as locks'' line alluded to the [[#Tracer_Trail_Cipher|Tracer Trail]] ciphertext being used as a key. |
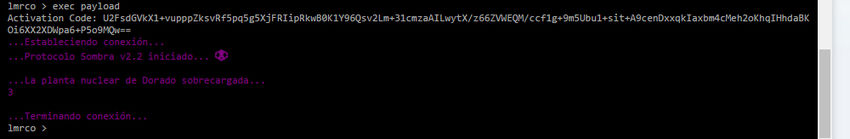
| − | Simultaneously, entering <code>exec payload</code> presented players with a prompt — the answer to which | + | Simultaneously, entering <code>exec payload</code> presented players with a prompt — the answer to which was the [[#Tracer_Trail_Cipher|Tracer Trail]]. When inputted, players were given a message that looked similar to what was previously seen at amomentincrime.com. The counter shown in the top right was then incremented. |
[[Image:LumericoTerminalTracerEntered.jpg|850px]] | [[Image:LumericoTerminalTracerEntered.jpg|850px]] | ||
| Line 675: | Line 705: | ||
[[Image:LumericoHacked.jpg|thumb|right|lumerico.mx website hacked by Sombra]] | [[Image:LumericoHacked.jpg|thumb|right|lumerico.mx website hacked by Sombra]] | ||
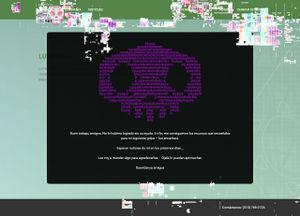
| − | On October 1, 2016, the lumerico.mx home page | + | On October 1, 2016, the lumerico.mx home page updated to show "glitches" and a black overlay with a message under a purple skull, and the string <code><!-- MISDIRECTION --></code> was also added to the source of the page. |
| − | The message | + | The message said: |
<pre> | <pre> | ||
| Line 688: | Line 718: | ||
Translated: | Translated: | ||
| − | < | + | <pre> |
| − | Good job, | + | Good job, friends. I would not have done it without your help. Anyway, I got the resources needed for my next hit - you'll love it. |
Expect to hear from me in the coming days... | Expect to hear from me in the coming days... | ||
I'm going to send something to thank you ... Hopefully you can use it. | I'm going to send something to thank you ... Hopefully you can use it. | ||
Dasvidanya friends | Dasvidanya friends | ||
</pre> | </pre> | ||
| + | |||
| + | |||
| + | |||
| + | Note that ''Dasvidanya'' is a phonetic transliteration of ''до свиданья'' — a Russian phrase for "goodbye". The thing that Sombra sent as a ''thank you'' was a new spray, named "Día de Los Muertos" after the Mexican festival that took place at the same time as the ARG. The spray is currently only available on the PC version of the game. | ||
[[File:Dia de los muertos spray.jpg|thumbnail|right|The Día de Los Muertos spray that was added to the game after Sombra hacked the Lumerico site]] | [[File:Dia de los muertos spray.jpg|thumbnail|right|The Día de Los Muertos spray that was added to the game after Sombra hacked the Lumerico site]] | ||
| − | + | The '''MISDIRECTION''' string lead to the MISDIRECTION [https://lumerico.mx/MISDIRECTION/index.html directory] which contained the text: | |
| − | |||
| − | The '''MISDIRECTION''' string lead to the | ||
| + | <pre> | ||
...Estableciendo conexiуn... | ...Estableciendo conexiуn... | ||
...Protocolo Sombra v2.3 iniciado... | ...Protocolo Sombra v2.3 iniciado... | ||
| Line 710: | Line 743: | ||
...boop ;)... | ...boop ;)... | ||
...Terminando conexión... | ...Terminando conexión... | ||
| + | </pre> | ||
Translated: | Translated: | ||
| + | <pre> | ||
...Establishing connection... | ...Establishing connection... | ||
...Sombra Protocol v2.3 initiated... | ...Sombra Protocol v2.3 initiated... | ||
| Line 722: | Line 757: | ||
...boop ;)... | ...boop ;)... | ||
...Ending connection.. | ...Ending connection.. | ||
| + | </pre> | ||
== Blizzcon == | == Blizzcon == | ||
Latest revision as of 23:20, 10 September 2020
| Sombra ARG | |
|---|---|
| The Sombra ARG - an ARG involving an unreleased Overwatch hero. | |
| Type | Official |
| Creator | Blizzard Entertainment |
| Discovered | 2016-06-12 |
| Completed | 2016-11-04 |
Main Page > List of Investigations > Sombra ARG
The Sombra ARG was an ARG for the first-person shooter Overwatch, developed by Blizzard Entertainment. Sombra was the name of a then-unreleased Overwatch hero. The ARG was comprised of clues and ciphers referencing Sombra, which were found in various developer updates and short animations.
At the game's release, there were numerous pieces of in-game information that appeared in the map Dorado, hinting at a character called Sombra. When the hero Ana was revealed, more Sombra clues appeared in Ana's origin video. In the weeks that followed, more clues were discovered, which led up to a character reveal animation at BlizzCon 2016.
Contents
Ana Videos
Ana Origin Video
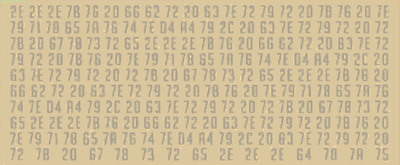
On July 12, 2016, a video for the new Overwatch hero named Ana was released. At the 1:16 mark, players discovered a set of hexidecmial values:
2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E 64 78 7A 75
A hex to ASCII translation yielded the following:
...{v fbr c~ryr {v ~yqxezvt~Ô¤y, c~ryr r{ gxsre...{v fbr c~ryr {v ~yqxezvt~Ô¤y, c~ryr r{ gxsre...{v fbr c~ryr {v ~yqxezvt~Ô¤y, c~ryr r{ gxsre...{v fbr
c~ryr {v ~yqxezvt~Ô¤y, c~ryr r{ gxsre...dxzu
Using an XOR Cipher with the constant 23 on the above text resulted in the following message:
..la que tiene la información; tiene el poder...la que tiene la información; tiene el poder...la que tiene la información; tiene el poder...la que tiene la información; tiene el poder...somb
This was a repeating phrase in Spanish, which translated to:
She who has the information, has the power...
Players then discovered a second set of hexidecimal values at the 2:11 mark:
65 76 2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E 7B 76 20 66 62 72 20 63 7E 72 79 72 20 7B 76 20 7E 79 71 78 65 7A 76 74 7E D4 A4 79 2C 20 63 7E 72 79 72 20 72 7B 20 67 78 73 72 65 2E 2E 2E
When put through the same process, the same string of Spanish was revealed, but with the letters ra at the beginning of the message. These letters were combined with somb from the first cipher to create the name sombra. No more clues were discovered until the release of the Dev Update video.
Dev Update Video
On July 19, 2016, the first Developer Update was released for Ana. At the end of the video, players discovered a series of vertical barcodes. When scanned, players discovered a large set of hexidecimal values which where then converted to binary, a dump of which is available here.
Turning the ones and zeroes into black and white pixels formed a QR code:
Scanning this QR code yielded the following message: ¿Estuvo eso facilito? Ahora que tengo su atención, déjenme se las pongo más difícil. In English, the message reads: Was that easy? Well, now that I have your attention, allow me to make things much more difficult. After this, no more clues were discovered until the Summer Games video was released.
Welcome to the Summer Games Video
Tracer Trail Cipher
Note: The cipher described below remains unsolved.
On August 2, 2016, players discovered another cipher in the Welcome to the Summer Games trailer:
U2FsdGVkX1+vupppZksvRf5pq5g5XjFRIipRkwB0K1Y96Qsv2L m+31cmzaAILwytX/z66ZVWEQM/ccf1g+9m5Ubu1+sit+A9cenD xxqkIaxbm4cMeh2oKhqIHhdaBKOi6XX2XDWpa6+P5o9MQw==
Players discovered this text to be base64 encryption. When decrypted, players received the following output:
Salted__���ifK/E�i��9^1Q�*Q�t+V=�
/ع��W/
�_����V��?q����f�F���"��=q�������[��
z��*����Z����u�\5�k�C
(Note: copy/pasting this string will not work; some of the characters are not printable and are not even displayed correctly on this page)
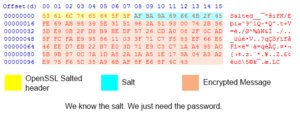
Decrypting the Cipher
The "Salted__" header at the start of the string indicated to players that the remainder of the text was encrypted with the OpenSSL software library, which requires a password and the encryption cipher that was used. Salt is added by OpenSSL to ensure uniqueness of the key and the IV derived from the password and used for the encryption. However, due to the age of OpenSSL and its massive library, it was proven to be quite difficult for players to identify the encryption used.
Narrowing Down Ciphers
Players narrowed down the potential ciphers used by examining a hex dump of the encrypted string. There are two major types of ciphers, stream ciphers and block ciphers. Stream ciphers encrypt only the data fed into them, whereas block ciphers always encrypt a certain number of bytes at a time (a "chunk").
A byte is roughly a single character, but special characters can take up multiple bytes. We know that OpenSSL Salted Encryption uses the first 8 bytes of the output for Salted__ and the next 8 bytes for the actual salt. The rest of the information is the encrypted message.
The immediately interesting thing here is that the encrypted message data stops 3 bytes short of a full chunk. This is a excellent indicator that the cipher used is a stream cipher (or a block cipher in CTR/OFB/CFB mode). This narrows the list of potential ciphers down significantly. This also means that the final string that Blizzard encrypted is less than 93 bytes!
This cipher remains unsolved, but it's speculated that Blizzard moved past the cipher by creating alternate puzzles.
Directions & Letters
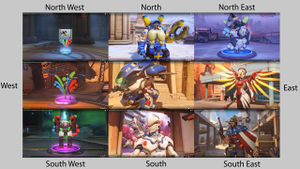
Players discovered that in the North American version of the Summer Games trailer there were repeated references to the cardinal directions, each associated with a particular hero. These references were conspicuously absent from other versions of the trailer. These references are shown below, with the relevant heroes and timestamps:
Screenshots of all the directions and their respective heroes can be found in an album here.
These heroes, arranged in this particular order, provided a password that was used later in the ARG.
Dorado Photo
At an unknown date, a new, "corrupted" photo of the Dorado attackers spawn point was added to the Overwatch media page. Players discovered that the screenshot was "datamoshed", which means it concealed a hidden message while also taking on a distorted appearance. (Here is an example of purposely data moshing the image manually to achieve similar effects.)
After comparing the images with difference checking tools, players found that certain English and Spanish characters were replaced with exclamation points. The missing characters produced the following Spanish phrase:
Por que estan mirando al cielo? La respuesta no esta sobre sus cabezas, esta detras de ustedes. A veces, necesitan analizar sus logros previos.
Translated into English, this phrase read:
Why are you looking at the sky? The answer isn't over your heads, it's behind you. Sometimes, you need to analyze your previous achievements.
The phrase "Why are you looking at the sky?" was most likely a reference to a strange artifact that was discovered in the sky of the Dorado map, dubbed the "Skycode". The Skycode ended up being a red herring, and was completely unrelated to the ARG.
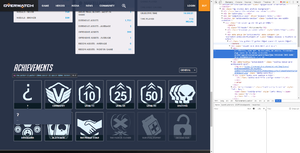
Analyzing Achievements
The phrase "you need to analyze your previous achievements" led players to look at the achievements on the Overwatch website. It was noticed that by logging in and viewing the achievements on a player profile, a mystery achievement appeared. Examining a hex dump of the image lead players to a new phrase:
Vientos, nada mal. No obstante, me aburro. Intentemos algo nuevo en la misma dirección. uczihriwgsxorxwunaarawryqhbrsfmeqrjjmu 5552E494 78T3 4VM9 OPL6 IS8208O913KRlrx
Translated, it said:
Damn, not bad. However, I'm getting bored. Let's try something new in the same direction. uczihriwgsxorxwunaarawryqhbrsfmeqrjjmu 5552E494 78T3 4VM9 OPL6 IS8208O913KRlrx
Volskaya Datamosh
After a long period of toying around, players discovered that the ciphertext uczihriwgsxorxwunaarawryqhbrsfmeqrjjmu 5552E494 78T3 4VM9 OPL6 IS8208O913KRlrx from the "?" achievement was a Vigenére cipher. Players discovered the key tracertorbjornwinstonsymmetradvamercybastiongenjimccree by ordering the heroes in the Summer Games trailer by the cardinal directions associated with each of them, as said further above. Once decoded, players received the following text:
blzgdapiproaakamaihdnetmediascreenshot 5552E494 78B3 4CE9 ACF6 EF8208F913CFjpg
Players found this to be a blzgdapipro-a.akamaihd.net/media/screenshot/5552E494-78B3-4CE9-ACF6-EF8208F913CF.jpg URL, which led players to a datamoshed screenshot of the Volskaya Industries map. (Editor's note: This link appears to now be dead). When players ran a difference check with the original image, they received an interesting message.
ASCII Skull #1
The diff from the datamoshed image resulted in the following output:
Parece que te gustan estos jueguitos... por que no jugamos uno de verdad?
:PB@Bk:
,jB@@B@B@B@BBL.
7G@B@B@BMMMMMB@B@B@Nr
:kB@B@@@MMOMOMOMOMMMM@B@B@B1,
:5@B@B@B@BBMMOMOMOMOMOMOMM@@@B@B@BBu.
70@@@B@B@B@BXBBOMOMOMOMOMOMMBMPB@B@B@B@B@Nr
G@@@BJ iB@B@@ OBMOMOMOMOMOMOM@2 B@B@B. EB@B@S
@@BM@GJBU. iSuB@OMOMOMOMOMOMM@OU1: .kBLM@M@B@
B@MMB@B 7@BBMMOMOMOMOMOBB@: B@BMM@B
@@@B@B 7@@@MMOMOMOMM@B@: @@B@B@
@@OLB. BNB@MMOMOMM@BEB rBjM@B
@@ @ M OBOMOMM@q M .@ @@
@@OvB B:u@MMOMOMMBJiB .BvM@B
@B@B@J 0@B@MMOMOMOMB@B@u q@@@B@
B@MBB@v G@@BMMMMMMMMMMMBB@5 F@BMM@B
@BBM@BPNi LMEB@OMMMM@B@MMOMM@BZM7 rEqB@MBB@
B@@@BM B@B@B qBMOMB@B@B@BMOMBL B@B@B @B@B@M
J@@@@PB@B@B@B7G@OMBB. ,@MMM@qLB@B@@@BqB@BBv
iGB@,i0@M@B@MMO@E : M@OMM@@@B@Pii@@N:
. B@M@B@MMM@B@B@B@MMM@@@M@B
@[email protected]@MBB@B@B@@BM@::B@B@
B@@@ .B@B.:@B@ :B@B @B@O
:0 r@B@ B@@ .@B@: P:
vMB :@B@ :BO7
,B@B
Translation:
"It seems you like these little games... Why don't we play a real one?"
(This is the python2 script to extract modified bytes from datamoshed Volskaya screenshot: https://gist.github.com/synap5e/27635d2ff6f0e3b15f0c902dca2974a9)
No further progress was made until August 23, 2016.
Overwatch Forums Glitching Page/ "Skycoder"
On August 23rd, 2016, at an unknown time, an ominous post by a user named "Skycoder" appeared on the official General Discussion forums for Overwatch.
Players found that the name of the post, 00110010 00110011, was binary for "23," which was a direct reference to Sombra being the 23rd hero in Overwatch. The age of the post started at 24 hours, and counted down rather than increasing. The post itself contained a single sentence in Spanish:
la que tiene la información; tiene el poder
Which, when translated to english, reads:
She who has the information, has the power.
After a short while, the post glitched and distorted, gradually turning a hue of purple. A text box then appeared, which printed the following ciphertext:
ICAgICAgICAgICAgICAgICAgICAgICAgICA6UEKPQms6CiAgICAgICAg ICAgICAgICAgICAgICAsakKIQEJAQkBCQEJCTC4KICAgICAgICAgICAg ICAgICAgIDdHlkKTQpVCTU1NTU1CQEJAQkBOcgogICAgICAgICAgICAg ICA6a0KSQpCIl01NT01PTU9NT01NTU2MQphCQEIxLAogICAgICAgICAg IDo1kUKNQphCiEJCTU1PTU9NT01PTU9NT01NipJuQm5CQEJCdS4KICAg ICAgICA3MG6GlUKIQpJClEJYQkJPTU9NT01PTU9NT01NQk1QQphCiEJA QkBCQE5yCiAgICAgIEeYlpdCSiBpQohCh4ggIE9CTU9NT01PTU9NT01P TZYyICBCj0JAQi4gRUJAQkBTCiAgICAgIJKWQk2HR0pCVS4gIGlTdUKI T01PTU9NT01PTU9NTZdPVTE6ICAua0JMTYhNhkKXCiAgICAgIEKMTU1C mUIgICAgICAgN4hCQk1NT01PTU9NT01PQkKWOiAgICAgICBCh0JNTYhC CiAgICAgII2YiEKKQiAgICAgICAgIDeSlkBNTU9NT01PTU1AQkA6ICAg ICAgICAgQEBCQEJACiAgICAgII+ST0xCLiAgICAgICAgICBCTkKPTU1P TU9NTY9CRUIgICAgICAgICAgckJqTYRCCiAgICAgIJBAICBAICAgICAg ICAgICBNICBPQk9NT01NQHEgIE0gICAgICAgICAgLkAgIEBACiAgICAg IISVT3ZCICAgICAgICAgICBCOnWMTU1PTU9NTUJKaUIgICAgICAgICAg LkJ2TUBCCiAgICAgIIRCkUKYSiAgICAgICAgIDCRQpdNTU9NT01PTUKV QkB1ICAgICAgICAgcUBAQEJACiAgICAgIEKETUJCjHYgICAgICAgR4+L Qk1NTU1NTU1NTU1NQkKINSAgICAgICBGhEJNTUBCCiAgICAgIIdCQk1/ QlBOaSAgIExNRUKFT01NTU2PQoNNTU9NTYpCWk03ICAgckVxQodNQkKE CiAgICAgIEKYloRCTSAgQm1ChEIgIHFCTU9NQpBChUKEQk1PTUJMICBC QEJAQiAgQEJAQkBNCiAgICAgICBKlm2GhFBCj0KEQplCN0eIT01CQi4g ICAsQE1NTUBxTEJAQkBAQEJxQkBCQnYKICAgICAgICAgIGlHQpUsaTCE TZZCbk1NT4tFICA6ICBNQE9NTUBAQEJAUGlpQEBOOgogICAgICAgICAg ICAgLiAgIEKXTZBCj01NTUBCQEJAQkBNTU1AQEBNQEIKICAgICAgICAg ICAgICAgICBAQkBCLmlATUJCQEJAQkBAQk1AOjpCQEJACiAgICAgICAg ICAgICAgICAgQkBAQCAuQkBCLjpAQkAgOkJAQiAgQEJATwogICAgICAg ICAgICAgICAgICAgOjAgckBCQCAgQkBAIC5AQkA6IFA6CiAgICAgICAg ICAgICAgICAgICAgICAgdk1CIDpAQkAgOkJPNwogICAgICAgICAgICAg ICAgICAgICAgICAgICAsQkBCCg==
ASCII Skull #2
Players discovered that this was Base64 and, once decrypted, resulted in another ASCII skull:
:PB.Bk:
,jBˆ@B@B@B@BBL.
7G–B“B•BMMMMMB@B@B@Nr
:kB’B.ˆ—MMOMOMOMOMMMMŒB˜B@B1,
:5‘B.B˜BˆBBMMOMOMOMOMOMOMMŠ’nBnB@BBu.
70n†•BˆB’B”BXBBOMOMOMOMOMOMMBMPB˜BˆB@B@B@Nr
G˜–—BJ iBˆB‡ˆ OBMOMOMOMOMOMOM–2 B.B@B. EB@B@S
’–BM‡GJBU. iSuBˆOMOMOMOMOMOMM—OU1: .kBLMˆM†B—
BŒMMB™B 7ˆBBMMOMOMOMOMOBB–: B‡BMMˆB
.˜ˆBŠB 7’–@MMOMOMOMM@B@: @@B@B@
.’OLB. BNB.MMOMOMM.BEB rBjM„B
.@ @ M OBOMOMM@q M .@ @@
„•OvB B:uŒMMOMOMMBJiB .BvM@B
„B‘B˜J 0‘B—MMOMOMOMB•B@u q@@@B@
B„MBBŒv G.‹BMMMMMMMMMMMBBˆ5 F„BMM@B
‡BBM.BPNi LMEB…OMMMM.BƒMMOMMŠBZM7 rEqB‡MBB„
B˜–„BM BmB„B qBMOMB.B…B„BMOMBL B@B@B @B@B@M
J–m†„PB.B„B™B7GˆOMBB. ,@MMM@qLB@B@@@BqB@BBv
iGB•,i0„M–BnMMO‹E : M@OMM@@@B@Pii@@N:
. B—M.B.MMM@B@B@B@MMM@@@M@B
@[email protected]@MBB@B@B@@BM@::B@B@
B@@@ .B@B.:@B@ :B@B @B@O
:0 r@B@ B@@ .@B@: P:
vMB :@B@ :BO7
,B@B
Players discovered that, once both skulls had been stripped of spaces, the bytes of each skull that aren't equal to 0 could be subtracted using a script. Once compiled, players received the following string:
OHVSURPHWLXQMXHJR...FUHRTXHXVWHGHVORVGHWHFWLYHVGHMXHJRVOROODPDULDQXQWUDLOKHDG?EOCJGDXVD-DPEDV-FDODYHUDV.KWPO
Players discovered that this was a caesar cipher. After shifting the string forward 23 places, it resulted in:
LESPROMETIUNJUEGO...CREOQUEUSTEDESLOSDETECTIVESDEJUEGOSLOLLAMARIANUNTRAILHEAD?BLZGDAUSA-AMBAS-CALAVERAS.HTML
When cleaned up, the message read:
Les prometi un juego...creo que ustedes los Detectives de Juegos lo llamarían un trailhead? BLZGDUSA-AMBAS-CALAVERAS.HTML
When translated from Spanish to English:
I promised you a game...I believe you Game Detectives would call it a trailhead? BLZGDAUSA-AMBAS-CALAVERAS.HTML
USA-AMBAS-CALAVERAS translated to USE-BOTH-SKULLS, and the .HTML extension hinted at a URL.
Skull Video
BLZGDA refers to the servers that Blizzard uses to host media on their website. As such, this led players to [ https://blzgdapipro-a.akamaihd.net/media/screenshot/usa-ambas-calaveras.html this page], which contains a video of a vitals screen depicting a skull and some other medical information. In addition, it also contained a graphic of one of the ASCII skulls. An Imgur mirror can be found here.
Within the properties of the video, players found another comment in Spanish:
Parecen estar muy interesados en estos "héroes". ¿Tal vez les interese conocer algunos detallitos que he averiguado sobre ellos?
In English:
You seem to be very interested in these "heroes". Maybe interested to know some details that I found out about them?
In addition, the video contains a heartbeat monitor, and a series of 26 lines above it. When players assigned the letters of the alphabet to the 26 lines, and used the "pings" of the heartbeat to determine what letters to use, the following string was found:
momentincrime
amomentincrime E-mail
'momentincrime' appeared to refer to the in-universe TV show "A Moment in Crime," which can be seen in the Roadhog and Junkrat video that came out months before the release of Overwatch. However, players also discovered a website, amomentincrime.com, and displayed the following text:
...Estableciendo conexión... ...Protocolo Sombra v1.3 iniciado... ...Infiltrando la respuesta automática del email de pistas... ...Terminando conexión...
Players discovered that sending an e-mail to [email protected] resulted in an automated email response:
Thank you for contacting A Moment in Crime's anonymous crime line! We have analyzed your submission and forwarded the information to the relevant parties. Your help could be vital in apprehending these cri ...Estableciendo conexión... ...Protocolo Sombra v1.7 iniciado... 01:07:47 02:02:02 01:08:06 02:13:43 01:18:32 01:18:21 02:10:19 01:06:21 02:05:18 01:04:02 01:07:08 02:18:25 01:13:04 02:19:20 01:23:02 01:16:40 02:16:35 01:23:04 02:17:16 01:06:42 01:13:29 02:18:06 01:05:02 02:15:41 01:08:34 j.7F57O,NLv:qj.7B:,1qv@B1j5ivB:, ...Terminando conexión... minals and bringing them to justice. These fugitives are responsible for a string of robberies, arson, and other crimes stretching from Sydney to King's Row. Authorities believe that they have set their sights on crossing the Atlantic to America.
Players discovered that, if the sets of numbers were taken as AA:BB:CC, where AA was the number of skull (in order of discovery), BB was the row and CC was the column (as seen here), and organized into a 5x5 matrix, it would result in:
S j G B L . @ M O k i , v : 0 E 7 r q N J P 5 F 1
Players discovered that this Matrix could be used as a bifid key to decode the text underneath the table of numbers in the email, as shown below:
j . 7 F 5 7 O , N L v : q j . 7 B : , 1 q v @ B 1 j 5 i v B : , 12 21 42 54 53 42 24 32 45 15 33 34 44 12 21 42 14 34 32 55 44 33 22 14 55 12 53 31 33 14 34 32 1 2 2 1 4 2 5 4 5 3 4 2 2 4 3 2 4 5 1 5 3 3 3 4 4 4 1 2 2 1 4 2 1 4 3 4 3 2 5 5 4 4 3 3 2 2 1 4 5 5 1 2 5 3 3 1 3 3 1 4 3 4 3 2 11 24 23 14 43 22 55 45 54 34 43 23 22 42 31 24 45 55 11 52 35 33 33 41 43 43 11 24 23 14 43 22
This gave players the following string:
SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@
This phrase was found to be leet-speak, and was translated to:
Sombra Information is power Sombra
The string SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@ was used as a password later on in the ARG.
A Moment in Crime Transmission
Once the 23-hour countdown on the Skycoder forum post reached zero, amomentincrime.com was updated. It now read:
...Estableciendo conexión... ...Protocolo Sombra v1.9 iniciado... ...Transmitiendo información a ómnicos activos... 2% ...Terminando conexión...
Translated from Spanish to English:
...Establishing connection... ...Sombra Protocol v1.9 initiated... ...Transmitting information to active omnics... 2% ...Ending connection...
A comment was also added to the source code:
Bien hecho, ya tienen mi clave. Hackear este programa de televisión no tuvo chiste. Espérense a lo que sigue.
When translated:
Well done, you have my password. Hacking this television program was meaningless. Wait for what is coming.
The percent on the amomentincrime.com slowly increased over time. Once the 5% milestone was hit, the Sombra Protocol version number changed to to v1.95. Afterwards, the percentage increased by 0.0038% every 3 minutes in real time.
In addition, another comment was added:
Parece que se están calentando un poco las cosas... tendré que pasar desapercibida mientras esto se finaliza.
Translated:
It seems things are heating up a bit... I'll have to go unnoticed while this is finishing.
On 18th October at 19:02 GMT the site reached 100%, and the site updated with the following message:
...Transmisión finalizada - finalizando carga... ...Carga finalizada. Unidad Bastion E-54 comprometida...
Which roughly translates to:
...Transmission complete - finishing upload... ...Upload finished. Unit Bastion E-54 engaged...
Hidden in the source code of the site was the text v1.4.0.2.324??. Players then correctly assumed that this referred to a future build of Overwatch itself.
Sombra vs. LumériCo
The Hacked Bastion
On October 19, 2016, a new Overwatch version was released - version 1.4.0.2.32448. Shortly afterwards, the version number in the source code of the amomentincrime site updated to the same version number. After the build launched, players discovered that the hero Bastion had a strange interaction when near the "SOMBRA PROTOCOL" monitors on Dorado, and would emit a message in morse code, which can be heard here. When the morse was decoded, players received the following string:
SQOFJFBNITIZWGDXSDO
Players discovered that this was a Vigenere cipher, and the key consisted of the alphabetic characters from the
SOMBr@1NF:rM@7iON1SP0vvErrSOMBr@ string, it was decoded to read:
ACCESSWWWLUMERICOMX
This led players to the LumeriCo website. (Editor's note: as of 2018, this site appears to be inactive.)
LuméReaction
The LumeriCo website was for the in-universe Mexican tech giant LumériCo, who had built several reactors in the Dorado region. The website had a news page, noting the imminent opening of a new reactor on November 1 as well as a recent attack on its construction site. There were also About and Login pages.
Players also discovered a robot.txt file, which appeared to server no purpose and only contained the text Allow: omnics, and appeared to be a joke about the Robots exclusion standard. Another text file was discovered called omnics.txt, which contained the text:
Allow: ?? Allow: ???
And appeared to be yet anotehr joke about the Robots exclusion standard. And, finally, an api file that contained {"message":"thanks for calling the api"} and, humorously, has no practical purpose.
Phone Number
At the bottom of the LumeriCo website, players discovered a phone number (510) 766-2726. When called, players heard a woman listing off a string of numbers in Spanish, a recording of which can be found here. The numbers spoken are: 5-2-4-1-3 (pause) 23-4-14-8-6-18-17-23-21-18-15.
When assuming that a=1, b=2, etc, the second part of the message can be decoded to: WDNHFRQWURO. This was found to be a ROT-23 cipher, and decoded to: TAKECONTROL.
Take Control
The phone message led players to an important page on the site, under the directory TAKECONTROL. It was styled the same way as amomentincrime.com and featured an image of Sombra's skull icon, named "calavera.png". There was also text on the page:
ethldtíoíesnoemfetuylm.bnlsssqtann)hcnslararuCpdGeoopéqubdsroaan.arnasdmdor1vrsmerñerlsdacnnnoaexedsidcn.iarsgcyi,iqeqnd.pooitoaeaaransterLetéáedasodocMrnseeiuCsimnosetlójnueodacapsadcoanfasest.rnucaodacadmdoemoipíogPoipbehaSussai.,yccandin.reueatenaoiorneoeetaoéyenimt¿rPehec,uurobudeílrysriteenasni,adngpjrálireecgrolsmhYnao?nmonomepeldezmapcpunoaulrrruCstmeitltetlróesoapsdéyufcuascaa,rensbuinergnqedlmvlbpdtaz.enebuineuldoerecrGefqfirrasulrbeatHsilnbaúaeeaaooassraooa,ioedo:aLiuielPr ursmoootlnielteeánlosulobeauaanopearrúiesltéyrosssisuaaeaenremsieaismdjmolrsspebiecdéyusittnvrcacp.taebrtLiunróporner eúcrneuyraarsettsyrseen.aaPnrneuyraeastuCpnhl/wLloaloa.qartlsyuínreute.evgdpiuábdmPooucvdeccmoreurr.o?unriorydbaSnalegeáezadienáutalaaioeemfcbgdinableoc¿éppoeocelsumuoaHearsosqadrrrftuLiorannnoneneriiatcnlomoqnaqdunrcno,enmerosaereisloabolii.e.dormerosepopdé,eo:r#5scoegaqoeaibs(edioraamtdírnlyoetjcgratmnrrobnrsstloeYqoeocicpnómlpernmaepogenmodqamubodnaeasuaenMoolloupeqvgrLtúr tsosrdvoeaerroaeusdmaauamoMobsnaeanraunnt,roierbeoiemaodbmantursotñauoureeuoerreopc.etlr sotñneerLimeaFsNJ
Players found this to be a column order transposition cipher with the key 5 2 4 1 3, which was found in the phone message. The cleaned up result was:
Los felicito por haber llegado hasta aquí. Solo quería saber si estaban listos. (Hey, es muy difícil encontrar buena ayuda últimamente...deberían ver algunos de los payasitos que están trabajando conmigo) Por ahora, continuemos con el verdadero reto: acabar con LumériCo y su president e Guillermo Portero. ¿Y porqué? Porque es un hombre codicioso, corrupto y un ladrón abominable. Su plan de traer en línea el más grande y el más poderoso zigurat el 1 de noviembre no es nada más que una artimaña, un elaborado plan designado para ejercer aún más influencia sobre la gente de México y en gordar los bolsillos de sus compinches. ¿Y quién va a pagar por eso? La gente común y corriente, los mismos que siempre quedan olvidados. He empezado a mejorar mis protocolos para que sean usados para derrumbar la infraestructura de LumériCo y Los Muertos también están intentando levantarse en contra de la corrupción. Mientras tanto, escarben por el sitio de LumériCo y busquen información que podamos usar en contra del cabrón, mejor aún, encuentren su nombre de usuario y contraseña para asegurarnos de que ciertos detalles no muy favorables sobre el presidentito...aparezcan... Pude encontrar el nombre de usuario y contraseña de un empleado de soporte de LumériCo, empiecen por ahí: GFlores/g#fNwP5qJ
Translated:
I'm congratulating you for getting in here. I only wanted to know if you were ready or not. (Hey, it's really difficult to get good help lately... you should see some of the clowns I'm working with). For now, let's continue with the true challenge: taking down Lumerico Corp president Guillermo Portero. Why? Because he's a greedy and corrupt man, and an abominable thief. His plan of bringing in line the most powerful and biggest zigurat the 1st of november us nothing more than a deceit, an elaborate plan by his gang to become even more influential in the people of Mexico and get more money. And who's gonna pay for that? Common people, the ones that are always forgotten. I've started upgrading my protocols so that they are used to take down the Lumerico Corp infraestructure and Los Muertos are also trying to go against the corruption. Meanwhile, search the Lumerico Corp site for info we can use against the bastard, or better, get his username and password so that hundreds "not so favorable" facts about the president start popping up. I was able to get the username and pass of a Lumerico Corp employee, start here: GFlores/g#fNwP5qJ
Presidential Login
Players used the credentials above on the Lumerico login page, and accessed the account of Gonzalo Flores, which included his emails. Transcripts of these emails were archived here.
However, only one email had relevance to the ARG:
De:Valeria Valderrama<[email protected]> Para:Gonzalo Flores<[email protected]> Asunto:Página de Guillermo Hola, Gonzo: ¿Puedes ver el tráfico de https://lumerico.mx/president-bypass? Guillermo debería ser el único accediendo desde su página de inicio privada, pero parece que está teniendo mucho tráfico. Tal vez tengamos que escalar esto a la señorita Jiménez, pero quiero estar segura de que es digno de su tiempo. Valeria Valderrama
The email referenced high traffic on the President Bypass Link. The page displayed an "access denied" message, but players found a President Auth-Bypass Revision 1.02: /.git/ line in the source code.
This line led players to dump the data from the /.git/ subpage with git protocol and upload it to Github. These were the code files behind the website, and included a class.authentication.php file that contained an encryption function, and class.president-bypass.php file which contained the president's (Guillermo Portero) username, GPortero, and encrypted password ?MzY:MTI5:?AzY:OWM?:?EDO:ZGU?:jVTM:MTJm:2ITM:MTUw:?QjY:OWY?:?kTO:MTQx:?MzY.
Some players wrote a function to decode the encrypted class.authentication.php file, and then used it on the encrypted password. The resulting password was Xy@4+Bkuqd<53uJ.
After logging in to the President's account, players were able to read his emails. After 30 minutes, another email appeared in the President's inbox, from Sombra herself:
Veo que se han podido infiltrar en su correo. No se preocupen, él no puede ver este correo, lo he ocultado de su vista si se conecta desde una de sus direcciones conocidas de IP. Necesito un poco más de tiempo para establecer el próximo grupo de potocolos. Manténganse atentos a principios de la otra semana. Le echaré unos cuantos trapitos sucios en sus correos para que se filtren al público "accidentalmente". Ya veremos como reaccionan los medios de comunicación.
The rough translation was:
I see you have been able to infiltrate into his mail. Don't worry, he cannot see this email, I've hidden it from his sight if he connects from one of his known IP addresses. I need a little bit of time to establish the next set of protocols. Stay alert early next week. I'll throw some dirty laundry in his emails that can "accidentally" leak to the public. We'll see how the media will react to that.
Admin Access
On October 25, 2016, new emails were discovered in the GFlores account, but they had no immediate significance to the ARG. In addition, omnics.txt was updated:
Allow: Tzolk'in Allow: Imix ChikchanManik Imix ChikchanImixChikchanImix Manik Chikchan Imix Kimi Chikchan Chikchan Kimi ChikchanImixChikchanImix ChikchanKimi
Tzolk'in is the name of a Mayan Calendar, and the second line was a series of animals from it in the Tzolk'in dialect. Imix stands for Day 1, Chikchan — 5, Manik — 7 and Kimi — 6. When turned into numbers, the string read 1 57 1 5151 7 5 1 6 5 5 6 5151 56. These digits turned into pictograms of Maya numerals (one by one, not numbers as a whole) written horizontally become . -..- . -.-. ..- - . .- - - .- -.-. -.- This was found to be morse code, and decoded to: EXECUTEATTACK.
This led players to the "EXECUTEATTACK" directory, where the following text was discovered:
Ha llegado el momento. Esos correos expuestos la verdad sobre Portero, iniciado la revuelta, y hemos convencido a la gente de México a apoyar nuestra causa. Ahora es el momento para el golpe. Convertiremos su preciada inauguración el 1 de noviembre en un gran movimiento en su contra. Necesito que hagan una cosa: Consigan acceso al correo del jefa de seguridad y busquen alguna forma de ayudarme en el ataque. Es posible que lo vean contactando a Portero pronto. He cambiado su contraseña a: d0r*NuLw9
Translated to English:
The moment has come. These emails exposed the truth about Portero, initiated the revolt, and have convinced people of Mexico to support our cause. Now is the time to strike. Convert his precious inauguration on November 1 to a large movement against it. I need you to do one thing: Get access to the email security chief and seek some form of help in the attack. You may see her contacting Portero soon. I've changed her password: d0r*NuLw9
Logging in with the credentials MJimenez / d0r*NuLw9 gave players access to the admin panel of the LumeriCo reactor. Until November 1, 2016, it stayed inactive and any command was answered with the same message saying that the terminal disconnected.
The Terminal
Once the console became usable, players could type help to see a list of commands:
override Engineer safety mode override help Provides help information about commands version Displays system version information about Displays information about the system grep Search output by string
In the MJimenez email account, there was an email labeled Corrupción de correo electrónico with highlighted text in side of it, specifically /ter/. Players discovered that performing the Linux command about | grep 'ter' in the console returned this text:
Open source lightweight shell for any terminal. Anything with a terminal 1.1.0 - expanded terminal support
The first word of every line given from the output was bolded and purple. Putting the letters together, players received the text OpenAnything1.1.0, which was a later solution.
Another available command for the terminal was override, and prompted players with three security questions:
- Favorite Movie. The answer to the prompt is
some like it bot, a movie from the Overwatch universe. - Favorite Cookie Flavor. The answer being
nuevas sabor delicias, a flavor referenced in an email in the MJimenez account. - Secret. The answer to this prompt is
OpenAnything1.1.0.
This returned OK, gave players admin access, and enabled a new set of commands:
ls Lists files by path cat Read file by path exec Execute a file
Typing ls listed two files: payload and d_ilqh_nhb.html (the file name was a ROT23 for a_fine_key).
cat mnt/d_ilqh_nhb.html yielded a text where ASCII characters (repeating string vhnl tldv xyl vcxelo xv qhrtv. zkolg[nl]) were in a shape of a key. Deciphering it using an Affine cipher (A=23, B=23) yielded the following string: some keys are shaped as locks. index[me]. It is assumed that some keys are shaped as locks line alluded to the Tracer Trail ciphertext being used as a key.
Simultaneously, entering exec payload presented players with a prompt — the answer to which was the Tracer Trail. When inputted, players were given a message that looked similar to what was previously seen at amomentincrime.com. The counter shown in the top right was then incremented.
Misdirection
On October 1, 2016, the lumerico.mx home page updated to show "glitches" and a black overlay with a message under a purple skull, and the string <!-- MISDIRECTION --> was also added to the source of the page.
The message said:
Buen trabajo, amigos. No lo hubiera logrado sin su ayuda. En fin, me consiguieron los recursos que necesitaba para mi siguiente golpe – les encantará. Esperen noticias de mí en los próximos días... Les voy a mandar algo para agradecerles… Ojalá lo puedan aprovechar. Dasvidanya amigos
Translated:
Good job, friends. I would not have done it without your help. Anyway, I got the resources needed for my next hit - you'll love it. Expect to hear from me in the coming days... I'm going to send something to thank you ... Hopefully you can use it. Dasvidanya friends
Note that Dasvidanya is a phonetic transliteration of до свиданья — a Russian phrase for "goodbye". The thing that Sombra sent as a thank you was a new spray, named "Día de Los Muertos" after the Mexican festival that took place at the same time as the ARG. The spray is currently only available on the PC version of the game.
The MISDIRECTION string lead to the MISDIRECTION directory which contained the text:
...Estableciendo conexiуn... ...Protocolo Sombra v2.3 iniciado... ...Desviando datos del zigurat de LumériCo hacia el objetivo... ...Descifrando contraseсas del objetivo... ...Acceso otorgado al directorio de volskayaindustries.com... ...boop ;)... ...Terminando conexión...
Translated:
...Establishing connection... ...Sombra Protocol v2.3 initiated... ...Forwarding the data from the LumériCo ziggurat to the target... ...Deciphering the target passwords... ...Access Granted to the directory of volskayaindustries.com... ...boop ;)... ...Ending connection..
Blizzcon
Blizzcon 2016 opened with the Overwatch short "Infiltration", a short depicting Reaper, Widowmaker, and Sombra on Volskaya Industries. During the showing of the short, Sombra's hero page went live, showcasing her abilities and character backstory.
References
Community Resources
A collection of tools and resources made by the Game Detectives Discord community for use in the ARG.
ASCII Skull
ASCII Skull Analysis: https://github.com/bahamas10/sombra
Removing SOMBR@ Analysis: https://pastebin.com/15u27YTC
ASCII Skull Eye Analysys: https://docs.google.com/spreadsheets/d/1-JQpWyitMKYhP-4l8ZDFiJI3NjqRrvoEnRdFQawike8
Google Docs
Observations and Speculations Spreadsheet: https://docs.google.com/spreadsheets/d/1rI08baFQmAwaqHC-9GF9VNGCYjuRE-q4LN9k4ottjuQ/pubhtml
LumériCo Emails and Translations Spreadsheet: https://goo.gl/cQgdIJ (Courtesy of UberPilot)
Tracer Code
GOL! Guesser: https://axxim.net/ow/gol-guesser/
Uber GOL! Guesser: https://axxim.net/ow/gol-guesser/uber/
The Uber GOL! Guesser only prints out UTF-8 compliant results, which makes it easier to identify potentially correct answers.
Bruteforcing tool: https://github.com/glv2/bruteforce-salted-openssl
Third-Party Resources
A collection of third-party tools and resources that the Game Detectives Discord community has used in the ARG.
Image of Reaper
stegdetect (Linux): https://github.com/abeluck/stegdetect
stegdetect is a Linux utility used to determine if a given image may contain encoded information.
JPHide & JPSeek: https://linux01.gwdg.de/~alatham/stego.html
iSteg (Mac OSX): https://www.hanynet.com/isteg/
JPHide & JPSeek is used to hide and find, respectively, a file inside a JPEG image.
iSteg works similarly to JPHide on the Mac OSX platform.
stegbreak (Linux): https://linux.die.net/man/1/stegbreak
stegbreak is used to do brute-force dictionary attacks on JPEG images.
Easter Eggs
The following are collection of references and Easter Eggs encountered throughout the ARG.
In-Game
Sombra's "Amused" Emote
This character emote features the Skycode, accompanied by soft music resembling the Skysong. Sombra's expression is one of amusement, and it's a nod to the community's prolonged creative attempts to solving an nonexistent puzzle.
Skycode Spray
This character spray features Sombra's iconic skull in front of a compass rose and the Skycode. This is a reference to both the cardinal directions used in one of the puzzles and to the Skycode, which is considered the most significant false lead that solvers encountered.
In-ARG
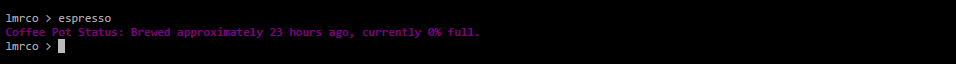
Espresso Command
There was a hidden command in LumériCo's admin terminal. Inputting the word espresso returned the following message: Coffee Pot Status: Brewed approximately 23 hours ago, currently 0% full
This is referencing a variety of emails found in the LumériCo site involving broken espresso machines and incompetent coffee brewing, which caught the attention of the community and gave way to a vast variety of mediocre jokes. Furthermore, "23 hours" makes reference to the number 23, which was believed by many to possess some sort of significance to the ARG, as Sombra would be the 23rd character in Overwatch. Finally, "0%" references the ARG's notable waiting periods that have been widely criticized by the community, specifically A Moment in Crime's upload percentage.
Due to the iconic purple text it is believed that this hidden command was created by Sombra herself.
Media Appearances
3rd Aug. 2016
[EN] Kotaku - Overwatch Fans Find New Clues About The Mysterious Hero Sombra
[EN] Polygon - Overwatch fans are trying to crack the latest mystery about Sombra
[EN] PCGamesN - Overwatch's Sombra ARG continues with new clues, but no solutions
[EN] Team-Dignitas - Who is Sombra? All facts and clues about Sombra
[FR] Gamewave - UN NOUVEAU CODE CACHÉ DANS LA DERNIÈRE CINÉMATIQUE D'OVERWATCH!
[EN] FollowNews - Overwatch Fans Find New Clues About The Mysterious Hero Sombra
4th Aug. 2016
[EN] PCGamer - Overwatch Summer Games trailer hides a mysterious secret
[SK] Sector - Nové Overwatch video obsahuje ďalšie tajomstvá
[EN] Gamerant - Overwatch Players Uncover More ‘Sombra’ Clues
[HU] Gamestar - Overwatch - újabb nyomok utalnak a még be nem jelentett hősre
5th Aug. 2016
[EN] Kotaku - Days Later, Overwatch Fans Can't Figure Out The 'Sky Code' Mystery
[NL] Gamersnet - Cryptische speurtocht naar Overwatch' nieuwe heldin Sombra gaat bizar diep
[ES] Alfa Beta Jeuga - Overwatch: El enigma de Sombra sigue ofreciendo nuevos detalles
[EN] IGN (Video) - Sombra: Overwatch's Secret New Hero - Overwatch HQ
7th Aug. 2016
[EN] Gamespresso - Summary of the state of sombra's ARG in Overwatch
8th Aug. 2016
[EN/CN] Zhentoo - Overwatch new hero Secret Dorado hidden mystery
[EN] TechNewsToday - Overwatch: Sombra Continues to Elude Detectives
11th Aug. 2016
[EN] The Know - New Overwatch Hero Hints
12th Aug. 2016
[EN] Kotaku - Overwatch Fans' Sombra Investigation Reaps A Skull Code
14th Aug. 2016
[EN] Gamerant - Skull Code is Latest Clue in Overwatch’s Sombra Investigation
16th Aug. 2016
[EN] Christian Today - 'Overwatch' DLC update: Skull Code the latest clue for Sombra investigation
[EN] Yibada - 'Overwatch' DLC update: New clues on Sombra's inclusion to the roster revealed
23rd Aug. 2016
[EN] Tech News Today - Overwatch: All We Know About the Sombra ARG
24th Aug. 2016
[EN] Gamerant - Overwatch Forums Glitch Out, Reveals Hidden Message From Sombra
[EN] Gamerant - New Website Counts Down To Next Clue For Overwatch’s Sombra
[EN] Polygon - Overwatch's Sombra mystery appears to be coming to a close
[EN] VG247 - Overwatch forums glitch out, reveal a message from the mysterious Sombra
[EN] Tech News Today - Sombra Hacks Into Overwatch Forums
[EN] IGN - Overwatch Mystery Character Sombra Could Be Revealed Today
25th Aug. 2016
[EN] Kotaku - Overwatch Players Are Getting Sick Of The Sombra ARG
[EN] IGN - Overwatch Made the Internet Lose its Mind Last Night, And I Had a Front-Row Seat
[EN] Tech News Today - Overwatch: Countdown to Sombra
30th Aug. 2016
[EN] PC Gamer - Overwatch's Sombra riddle begins to irritate the players trying to solve it
3rd Oct. 2016
[EN] Mobile & Apps - Sombra To Be Revealed At Blizzcon? Halloween Event Confirmed In Data Leak
4th Oct. 2016
[EN] iTechPost - Overwatch Update: Are We Finally Getting Sombra?
11th Oct. 2016
[EN] Kotaku - Overwatch Fans Hacked Actual People In An Attempt To Find Sombra
17th Oct. 2016
[EN] TelKom Gaming - Will Sombra Hack Her Way Into BlizzCon 2016?
18th Oct. 2016
[EN] OverwatchTips - Everything You NEED To Know (Sombra ARG)
26th Oct. 2016
[EN] Min Network - Everything we know about Blizzard's rumored Nov. 1 release
28th Oct. 2016
[EN] Kotaku - Imagining Horror Stories Of A Never-Ending Overwatch ARG
1st Nov. 2016
[EN] IGN - Will Sombra be at BlizzCon 2016?
8th Nov. 2016