HELIOS
| This page is a work in progress and will be updated as new developments emerge. If you have information you think should be added, please create an account to enable page edits or contact a Wiki Editor. |
| DSCS III A3 | |
|---|---|
| The Department of Defense has declassified access via uplink to the DSCS 3 satellite. Good Luck and Godspeed. | |
| Type | Official |
| Creator | Alice & Smith |
| Discovered | 2021-12-05 |
Main Page > List of Investigations > HELIOS
The DSCS III A3 ARG is an ongoing ARG by Alice & Smith. The initial trailhead notes that access that a US Department of Defense communications satellite has been authorized.
Day 1
At 03:24 on 2021-12-05, the Alice & Smith (A&S) Twitter account tweeted "WARNING - DSCS III A3 access has been authorized. Good Luck and Godspeed." with a link to the A&S Discord.
This was followed up at 17:05 with a second tweet stating "UPDATES | Dec 5th | - DSCS III A3 IRC TOR uplink and RTMP FEED updated to version 636f-rev1.". The reference to an RTMP feed led players to a Twitch stream titled HELIOS Task Force on the dscs_iii_a3 channel.
The stream contained an interactive terminal which users could enter commands into and get responses from. The initial terminal upon loading the stream was:
Setting hostid: 636f-rev1... Entropy harvesting: interrupt ethernet Fast boot: skipping disk checks Mounting remote file systems Starting network: DVB-TEXT DSCS-III-A3 Uplink Parameters: 7600 mhz - 7604 mhz Additional TCP/IP options: .sgov=1 Starting IRC TOR PID Manual: www.intelink.sgov.gov/wiki-ts/cmd-636f Starting background file system check in 60 seconds
Clicking on the icon to the right of the stream for the Helios terminal popped up a Twitch window describing it. This included a note saying that the command HELP should be used to start. Entering this into the terminal resulted in:
Available commands: version coredump help <ACCESS DENIED> <ACCESS DENIED> <ACCESS DENIED> Enter ‘help <command>’ for more information
Typing in help version and help coredump resulted in the following:
help version Command help for: version Displays the version details for DSCS_III_A3 help coredump Command help for: coredump Output a module's memory state Enter ‘coredump <module>’ to execute
Players then ran the version command, which gave them a hexadecimal code output.
DSCS_III_A3 Version 63 6f 6d 6d 61 6e 64 20 27 71 75 65 72 79 27 20 73 75 70 70 6f 72 74 20 3d 20 31 00
Converting the hexadecimal code to text produced the message command 'query' support = 1. This new command could be confirmed by typing in help query
Command help for: query Displays data relating to query subject Enter ‘query <module>’ to check for system status Latest system inventory: chks1029
By querying the latest system inventory noted on the last line of the output, players received info regarding several key systems:
ERROR: chks1029 format type table 31575 | Factory Main Door 25798 | Security Terminal 75879 | Main Control Room 59579 | Nuclear Blast Door 99879 | Lights Out Factory 65548 | Assembly Line Alpha 65549 | Assembly Line Beta 65550 | Assembly Line Delta 65551 | Assembly Line Gamma 75998 | Site Alpha Invalid query for module 'chks1029'
Attempting to query most of the provided ID numbers would result in unknown commands, however entering query 31575 would output:
Query Module 31575 Status Request - Factory Main Door Authorized commands: execute 31575 -open -<door access code> execute 31575 -close -<door access code> Please stand by... Module Status: Online
Players who ran the command coredump 31575 would be provided with a list of 9 pages of data to sort through.
WARNING: memory coredump for 31575 Generating files... 180 entries / GRID 20 by 9 coredump -read 31575.page1 coredump -read 31575.page2 coredump -read 31575.page3 coredump -read 31575.page4 coredump -read 31575.page5 coredump -read 31575.page6 coredump -read 31575.page7 coredump -read 31575.page8 coredump -read 31575.page9 Process successful
Entering these commands into the terminal would provide the data detailed below.
Coredump 31575 Pages
Page 1 provided three "blocks" of three-number digits, each arranged in a 5x4 grid.
Page 2 provided a list of colored books, seen below, with years as file extensions. The use of these "books" and years is currently unknown.
Memory Coredump PAGE 2 Module 31575 Blue book repo /repo/bb /1955 /1958 /1961 /1969 Yellow book repo /repo/yb /1971 /1976 /1980 Red book repo /repo/rb /1982 /1983 /1985 /1991 /1993 /1996 /1997 Green book repo /repo/gb File access denied [End of file]
Page 3 initially provided nothing, until some time estimated around 01:00 UTC, when it would update to read the following.
Memory Coredump PAGE 3 Module 31575 Audio Frenquency Render Completed 12-05-2021-16h17m28s [End of file]
Page 4 provided another set of three number "blocks", just as Page 1 did.
Page 5 provided a unique encrypted text detailed below.
Memory Coredump PAGE 5 Module 31575 Buffer Available 7e 20 38 20 64 61 79 73 20 74 6f 20 45 4c 45 [End of file]
Decoded, the hexadecimal string read ~ 8 days to ELE . "ELE" is currently believed to stand for "Extinction Level Event".
Page 6 provided five IRC/RTMP addresses, detailed below. The purpose of these addresses are currently unknown.
Memory Coredump PAGE 6 Module 31575 OPEN SOCKET 14321535.relay.nsa.sgov 14154789.relay.defense.sgov 14545787.relay.nevada.intelink.sgov 14998541.relay.rtmp.twitch.tv 14516555.relay--DVB-TEXT-IRC/.onion [End of file]
Page 7 is currently empty. If it is updated, so will this line.
Page 8 provided the third and final set of number boxes. These three sets of number boxes would soon be used to solve the first proper puzzle.
Page 9 provided a status screen of the satellite, detailed below. As of the first ~10 hours of the ARG, it read the following.
Memory Coredump PAGE 9 Module 31575 STATUS dscs_iii_a3 | access granted Control Door | awaiting command Station 1 | booting ~ 24h Control Room | access denied [End of file]
Should this change, the changes will be documented.
Day/Phase 1: SecretKey Solve
Following some hours of nothingness, players began to notice quirks within the livestream's audio. A series of sharp and deep tones would continuously repeat, to which players began to document.
The series would play Sharp, Two Deep, Sharp, Three Deep, Sharp, Five Deep, Sharp, Seven Deep, Three Sharp. The series would then repeat.
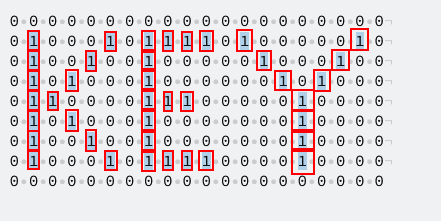
A keen-eared player noticed the tones corresponded to the first four numerical prime numbers, Two, Three, Five, and Seven. Using the "blocks" provided by the coredump pages 1, 4, and 8, a central superblock was formed utilizing earlier information from the initial coredump command, stating a "20x9 grid". Within this grid, substituting all non-prime numbers for zeroes, and all prime numbers for ones, a grid of zeroes and ones was formed, and when turned to it's side, spelled the word KEY.
The solve led to the completion of the command execute 31575 -open -key, which, when entered, would return the following.
Accessing local PGP Key /home/31337/.ssh/31575 Access authorized Requests received so far: 0 Connecting to module 31575 TAK1 - Valid TAK6 - Valid BGD8 - Valid DTB3 - Valid SDD4 - Valid Adding your entry, please wait... Process completed.
Note the line which says Requests received so far: 0. This is what it stated upon the first entry of the command, with every subsequent entry counting up by one. At the time of writing, it is believed the ARG will continue when enough people have entered the command, further backed up by the broadcasting account's messages in chat, claiming Module 31575, the factory door, to require "More Resources".
Every 25 entries, a routine camera check would be initiated, showing more of the facility to the livestream. As of writing, three camera checks have been performed, each revealing new areas of the facility. Currently, over 100 entries have been submitted, with no new goal yet confirmed.


