Inside ARG
| Inside ARG | |
|---|---|
| The Inside ARG revolved around mysterious codes being printed and deciphered. | |
| Type | Official |
| Creator | Playdead |
| Discovered | 2016-06-29 |
Main Page > List of Investigations > Inside ARG
INSIDE is a puzzle platforming game created by Playdead. After the game launched on June 29th, 2016, players noticed a printer in the background of one of the game areas. This printer was quite notable - on PC, the printer printed sequences of characters that are referred to in the game files as "Morse", despite the fact that these messages do not form legible Morse code. On other platforms, the printer formed other messages, some of which have already been deciphered.
Throughout this article, information has been taken from this Google doc.
Contents
Printer Strings
If you load the 12th last checkpoint and head to the left, there will be a printer in the background. Normally, it will print nondescript pages, but if the player walked in front of it and then wait roughly 10 seconds, it will begin to print a sequence of pages with large, visible symbols, which vary by platform. These are not randomized strings, but turn out to be chosen from a list of predetermined strings. Each platform prints from a different pool of strings.
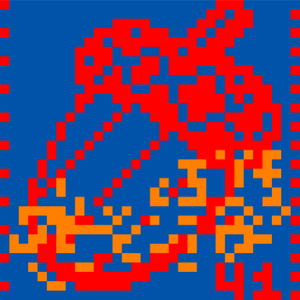
PC/PS4
On PC and on the PS4, the printer will display one of the following 41 strings, composed entirely out of dots dashes and slashes, apparently at random. Of these strings, 32 of them are 32 characters long, and 9 are various shorter lengths. This was the first set of printer codes discovered, and were present in the game at release.
-------------------------/-///-/ ----------------------//-//----/ ------------////-----//-///----- ---------//-/////////-///------- --------/----/-////-////--////-/ --------//--//////-/////-/-//--- --------//-//-//-----//-/-//---- --------///-/-///-///--////----/ --------////-//--//-////-------/ ------/----/-----///--//-///-/-/ ------/---/------/-//////-/-//-- -----/--/------/-----//./-./..-- ----.-//////////-------/-/-//--/ ----/--/------/----...///.//.--/ ---.-///../---////-..--/-/--/--- ---/-/.-----/----.-/..--/.--.--/ ---//-.----/----.-/--.--/----.-- --.....-.--.-.--------/.--.---.- --./-...//--.--/.--..//-/.-.-.-/ -.-.././----..----./.--.--...--/ -...//..----.---..//.--.-..----- /----------------------///------ /---------////-///--//-///-----/ /--------/////--//-////-/////--/ /-------/-//---//-///////------- /------/----/---///-//--////-/-- /----..-//////---------///--/--- /----/---/------/---/////////--/ /---/-/------/------.---/.-...-- /---//----//-..-///-----.------/ /--/----.-/-----..-...//..--..-/ /--/.-......--.------//....----- -------. --/. -.-.- -.-.-.-.-.- -.-.-./// -.-./ .-.--..-.-.-.-/ .-.-.-.-./// /.-.
Solution
The ASCII lines can be rearranged to form art of an acorn, with "41" in the bottom right corner.
On April 13, 2019, the string "LIFEDETECTED" was guessed and entered in the Playdead website. The PC/PS4 code has yet to be deciphered into this supposed solution.
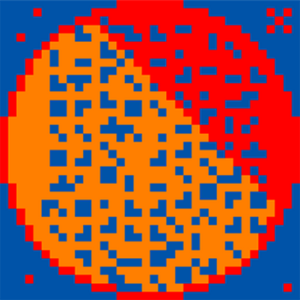
Xbox One
On Xbox One, the printer will display one of the following 47 unique strings. Of these strings, 35 of them are 36 characters long, and the remaining 12 are a variety of lengths, shorter than 36. At this time, their meaning has yet to be determined. These codes were discovered in June 2018 and it is unknown whether they have always been present or if they were added at some later date. Note that one of the strings was observed to occur about exactly twice as often as the rest. Additionally, including it in the list brings it up to 36 strings that are 36 characters long each, similar to how the PC strings have 32 strings that are 32 characters each.
--------------////////-------------- --------------////////-------------- -----------///---..-..///---------/- ---------///-//////////////------/-- -------//-../---//-//--//////---/-/- -------//...--.......--.--.//------- ------/...-...---.--...-.-.../------ -----/...--..-....---.......-./----- -----/......-.///////////-/-///----- ----/------//////////////-------/-/- ----/.-.....--.-/////-//////-///---- ----/.......-.......--.-...-.../---- ---/-----//..--...-..--..//--------- ---/..-..--...-.//--/////////////--- ---/..-...-.--.-..-..-.....--.--/--- ---/...-.--....--.--...-.......//--- ---/........--.../////-/--////-//--- --/---/..--..//--/--/////-////------ --/..-.-.--....--.--....-......../-- --/...--.-......-.-///////////////-- --/...-.---.-..-..///--////--/--//-- --/..........-......-..-.-..-.-.//-- -/...--..--.-..-...-.--....-..--.//- -/....---......-..--....--.....////- -/....--.--.--.--.-../-////---/////- -/....--.-.....--..-..//--/////////- -/..........-......./-//-////--////- -/....................-.--.--.--///- /.....--.--...-...--....-...//////// /.....--..-..-.....-.--...-//---//// /.....-..-..----.....--.///-/-////// /......-.-..--.-......-...---./-//// /......-..-...-.-..-...../////////// /...........--.......-...-..-/-///// /...........-.........-.--/-//-///// /............-........./-//-//-///// ---.-.--------.-.--.----.--- -..-.--..----..-.... .-.--.....-.-.-------..-.- .-.-.-.------------ .-..---....--.-.--- .-..-.-.-.-- .-..-.-.-.-............... ..-.------..-.- ..-.-.--.-....-- ..-.-.-.-.-... ...-.-.-.-....... .......--------
Solution
After looking carefully for patterns, it was discovered that the strings could be arranged to form an ASCII circle which serves as a scheme to give every code a definite position in the order. This explains why the reoccurring line occurs twice as often: the top and bottom of the circle happen to be perfectly identical.
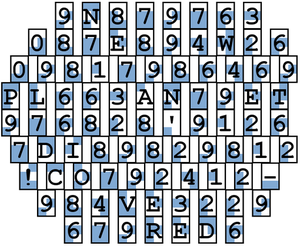
When rotated 90 degrees clockwise, players recognized Braille overlaid across the circle. When isolated from the ASCII image and decoded, the following strings are found:
9N879763 087E894W26 09817986469 PL663AN79ET 976828'9126 7DI89829812 !CO792412- 984VE3229 679RED6
By replacing the "!" as "S" and then isolating the letters, you get the password:
NEWPLANETDISCOVERED
This phrase, when entered on the main Playdead page, turned out to be a valid passcode. (See "Printer Button" for more information.)
iOS
On iOS (iPhone and iPad), the printer will display one of the following 24 strings. The string chosen is determined by the iPhone's local system time - they are ordered below in terms of when they'll appear on the printer. For instance, the first line will appear from 00:00 to 00:59.
⬛⬜⬜⬜⬛⬛⬛⬜⬛⬛⬛⬜⬛⬜⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛ ⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬜⬛⬛⬛⬜ ⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬛⬛⬛⬛ ⬛⬛⬛⬛⬛⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜ ⬜⬛⬛⬛⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬛⬛⬛⬜ ⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜ ⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬛⬛⬛⬛ ⬛⬛⬛⬛⬛⬛⬜⬜⬜⬜⬛⬛⬛⬜⬜⬛⬜⬜⬜⬜⬛⬛⬛⬛⬛ ⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜ ⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛ ⬜⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬜⬛⬛⬛⬜ ⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜ ⬛⬛⬛⬛⬛⬛⬜⬜⬜⬜⬛⬛⬛⬜⬜⬛⬜⬜⬜⬜⬛⬛⬛⬛⬛ ⬜⬛⬛⬛⬛⬛⬜⬜⬜⬜⬜⬛⬛⬛⬜⬜⬜⬜⬜⬛⬛⬛⬛⬛⬜ ⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜ ⬜⬛⬛⬛⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬛⬛⬛⬜ ⬜⬛⬛⬛⬛⬛⬜⬜⬜⬜⬜⬛⬛⬛⬜⬜⬜⬜⬜⬛⬛⬛⬛⬛⬜ ⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜ ⬜⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬛⬛⬛⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛ ⬛⬛⬛⬛⬛⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜⬜⬜⬛⬜⬜ ⬜⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬜⬜⬜⬜⬛⬜⬜⬜⬛⬜⬛⬛⬛⬜ ⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬛⬛⬛⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛ ⬛⬛⬛⬛⬛⬛⬜⬜⬜⬜⬛⬛⬛⬜⬜⬛⬜⬜⬜⬜⬛⬛⬛⬛⬛ ⬛⬛⬛⬛⬜⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬜⬜⬜⬛⬛⬛⬛⬛⬜
Solution
Each string is comprised of 25 characters, and can be divided into 5 segments of 5 characters each. For instance, the first string can be split up as follows:
⬛⬜⬜⬜⬛ ⬛⬛⬜⬛⬛ ⬛⬜⬛⬜⬛ ⬛⬜⬜⬜⬛ ⬛⬜⬜⬜⬛
Stacking these segments into a 5 by 5 grid yields the letter 'M' in the form of the following pattern:
⬛⬜⬜⬜⬛ ⬛⬛⬜⬛⬛ ⬛⬜⬛⬜⬛ ⬛⬜⬜⬜⬛ ⬛⬜⬜⬜⬛
Repeating this process for each string yields the following message:
MULTIPLEPROBESDISPATCHED
This phrase is another valid passcode on the main Playdead page.
Switch
On Nintendo Switch, the printer will display the following string:
⬛⬛⬜⬛⬜⬛⬛⬜⬛⬜⬜⬛⬛⬜⬜⬛⬜⬛⬛⬜⬛⬜⬜⬛⬜⬛⬛⬜⬛⬜⬛⬜⬜⬜⬛⬛⬜⬛⬜⬛⬛⬜⬛⬜⬜⬛⬛⬜⬛⬛⬜⬛⬛⬜⬜⬛⬛⬜⬛⬜⬜⬜⬛⬛⬜⬛⬜⬛⬜⬜⬛⬜⬛⬜⬜⬛⬜⬛⬜⬛⬜⬜⬛⬛⬜⬛⬜⬛⬛⬜⬛⬜⬜⬛⬛⬜⬛⬛⬜⬛⬛⬜⬜⬛⬛⬜⬛
The Nintendo Switch string can be translated to Morse code as follows:
⬜⬜⬜ -> / (a long pause between words) ⬜⬜ -> (a shorter pause between letters) ⬛⬛ -> - (long Morse character) ⬛ -> . (short Morse character) ⬜ -> (pause between Morse characters)
Decoding this Morse yields the following message:
CTRL CON DISCON
This turned out to be a hint as to the next part of this puzzle. After the printer is done printing the above morse message, it returns to printing grey pages. If you stay and disconnect and reconnect one of the controllers on your Switch, it will elicit a response from the printer. It will print a series of white pages or a single black page. By disconnecting and then reconnecting your controllers in the sequence RRLRLL, the printer will print consecutive white pages for each correct input in the sequence, until on the sixth input where it will print 6 white pages followed by a long morse message that decodes to a message in the following format:
R*G*B* R*G*B*"
Where the asterisks are a single digit number. After some experimentation, it was discovered that these codes corresponded roughly to the color of the left and right Joy-Cons (in that order) on the Switch. Switch Joy-Con controllers have an internal value that determines what color the system represents it as in the software, which INSIDE uses to determine what color your controllers are. This value can actually be edited using third party tools. With some research, it can be determined that there are six official Joy-Con colors, not counting promotional Joy-Cons. The following is each of these colors matched to the code that the printer gives for that color:
Blue Red Grey Pink Green Yellow R2G2B6 R3G1B1 R3G3B3 R5G1B5 R1G4B1 R3G3B0
Entering these codes into the Playdead website seemingly caused this section of the printreqstatus pages to be filled out with Xes:
+-+Comms. auth. req. schem[3] | | [X] [X] [ ] [ ] [ ] [ ] | +-+
It is hard to be sure what actions caused what, though, due to the chaos of the discord community at the time. After the dust cleared, printreqstatus pages 8 through 12 had been triggered to appear on the terminal41 website, and all six boxes have been filled.
Printer Button
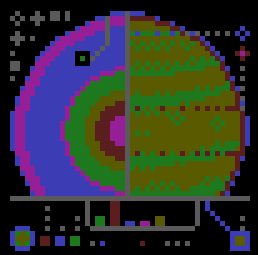
On June 4th, 2018, it was noticed that a printer button had been added to the Playdead website, next to its social media icon links. Clicking this button allows you to print the page. On the main page, the printout contains added text not present on the webpage. If the 'Subscribe' field is empty when the button is pressed, the message says "no message received". Any other input returns the message "incorrect message received". When the iOS printer codes were cracked to produce the string "MULTIPLEPROBESDISPATCHED", it turned out that entering that string into the website returns a printout of this image:
Shortly after the same time that this new code was entered into the website, the breachlog.html page on the terminal41.link website was updated with a reference to the new pages printreqstatus_005 and printreqstatus_006.
If an email address is entered into the subscribe field before hitting the printer button, sometimes an email will be sent to that email from the address "[email protected]". This is very inconsistent and it doesn't seem like anybody is getting these emails any more.
Later it was found that entering any of the "NEWPLANETDISCOVERED" / "LIFEDETECTED / "MULTIPLEPROBESDISPATCHED" codes in the Playdead website, one after another and in no particular order, gives three different printouts.
The RGB lines in the first printout image translates to binary (with GREEN = 1, BLUE = 0, RED = space). The binary then translates to the following ASCII string:
warning |factor 1 security passed| - |[] factors remaining| warning
Translating the second printout image in the same way gives this string:
warning |factor 2 security passed| | [error] factors remaining| warning
The third printout appears to be an artwork for the upcoming Playdead's game. There is also a spectrogram image embedded in the artwork that can be converted to sound with photosounder or an equivalent tool. This sound has been converted from the spectrogram, this is the transcript:
all system req breached all system check safety check systems checked - all systems ok systems checked - auxillary systems ok systems checked - secondary systems ok systems checked [?] - 98% breach status breach success damage status 0 mission status unknown mission estimated time of conclusion unknown mission status hold lock all hold lock error temporary shutdown procedure required auto shutdown procedure connect to repo-comms-gate-98-connect."ERROR"
The last line of the audio refers to this url http://www.terminal41.link/comms/gate/98/connect.html. The page contains a 2048x4096 pixels image, isolating all the pixels containing the exact RGB value #000000 reveals a series of pixels spaced at intervals of 16 pixels each in the top left. Doing the same with six other RGB values and overlapping them gives the following text:
REPO/SYS/ACTIVATE_SHUTDOWN_PROTOCOL/PROT6y723g90ty9r80234
Only capturing the pixels at those regular intervals of 16 shows what appears to be a scanning of a planet.
That leads us to this url http://terminal41.link/sys/activate_shutdown_protocol/PROT6y723g90ty9r80234.html which in turn leads to this one http://terminal41.link/sys/activate_shutdown_protocol/opts/confirm_shutdown_routine.html
Youtube Stream
The address "[email protected]" belongs to a gmail account with the name "Anthony T. Setrinamairé". Googling the last name, at the time it was first discovered, returned a single google result: this youtube stream. This stream has been offline ever since it was first found. There was a theory that having 20 people waiting on stream could cause the stream to start. This was disproven when 20+ people gathered at once and nothing happened.
Terminal41
Googling the string "terminal41" from the youtube string led to this webpage. When it was first discovered, the base page terminal41.link led to a redirect trail that eventually landed you on this page. Around that time, the source of every page along the redirect trail was checked, but there was nothing to find.
On June 24th, 2018, the following pages were batch modified. The following are the page sources as they were at this time:
terminal41.link/loadSys/__.html
terminal41.link/loadSys/___________DONE.html
terminal41.link/loadSys/LOAD_COMPLETE.html
Before these pages were modified, they were the same except everything in the "pre" tags weren't there. The unusual text in these pages is still a mystery.
The "__.html" page led to the discovery of two additional valid pages:
terminal41.link/sys/
terminal41.link/dat/
Both pages redirect to the main page, and their source is identical. The only notable thing about them is that their title differs from the rest of the pages: "/emergency terminal link [41]/ comms redir - aux. dir conf."
On the 25th of June, the last page in the redirect chain was modified:
view-source:terminal41.link/loadSys/LOAD_COMPLETE.html
Everything in the "pre"> section was removed, and the page now redirected to this previously unseen page:
terminal41.link/comms_main_viewgate_002.html
This page contained references to another new page:
terminal41.link/dat/breachlog.html (this page has been modified several times since. at the time it ended at the entry dated 25062018)
The breachlog page has been preiodically updating with new entries, along with references to these pages:
terminal41.link/sys/printreqstatus.html terminal41.link/sys/printreqstatus_002.html ... terminal41.link/sys/printreqstatus_007.html
These pages all appear to have been untouched since they were first added, and by referencing the breachlog it can be inferred what day they were uploaded. They seem to be a specification of 4 different passwords, called "schem.". Notably, the first two pages only had 3 schemes, but contained a line referring to an "exp." that would occur on June 28th, 2018. On this date, the Nintendo Switch port of INSIDE was released, and printreqstatus_003 was updated with a 4th scheme. Considering the fact that there were 3 different types of printer codes before this date, and that the switch version was confirmed to introduce a 4th type, it seems clear that each scheme refers to one of the INSIDE ports and the type of password that can be retrieved from their puzzles.
When the iOS puzzle was solved and its solution entered into the Playdead website, it seemingly caused the printreqstatus_006.html document to appear. This document seems to state that one of the four puzzles was indeed solved.
Besides printreqstatus_006, it cannot be proven that any of the changes to the website are due to the players' actions.
Interpretations: breachlog.html seems like it MIGHT be a counter for every time the printer button was pressed on the playdead website. However, this doesn't quite make sense because of these two entries:
>log(25042018)//breach attempt status//......[4] >log(11062018)//breach attempt status//......[4]
which suggests that nobody touched it between April 25th, 2018 and June 11th, 2018 which is demonstrably false. This might just be because the counter is kind of funky, but it's hard to say. Whatever it's counting, it's something that really spiked since June 11, 2018.
It's worth mentioning that the change between viewgate and viewgate_002 seems to suggest that there was some sort of success gaining access, but it is unknown what was done to achieve this.
All known pages, and their modification dates as of July 5th, 2018:
:Fri, 01 Dec 2017 15:07:52 GMT /loadSys/:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/_.html:Fri, 01 Dec 2017 15:10:08 GMT /loadSys/__.html:Sun, 24 Jun 2018 18:42:47 GMT /loadSys/___.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/____.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/_____.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/______.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/_______.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/________.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/_________.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/__________.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/___________DONE.html:Sun, 24 Jun 2018 18:39:19 GMT /loadSys/LOAD_____.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/LOAD_COM.html:Fri, 01 Dec 2017 15:10:07 GMT /loadSys/LOAD_COM_____.html:Fri, 01 Dec 2017 15:10:08 GMT /loadSys/LOAD_COM-----.html:Fri, 01 Dec 2017 15:10:08 GMT /loadSys/LOAD_COMPLETE.html:Mon, 25 Jun 2018 11:06:44 GMT /comms/ /comms_main_viewgate.html:Thu, 07 Dec 2017 15:40:23 GMT /comms_main_viewgate_002.html:Mon, 25 Jun 2018 11:05:57 GMT /sys/:Sun, 24 Jun 2018 18:35:57 GMT /sys/printreqstatus.html:Mon, 25 Jun 2018 11:08:05 GMT /sys/printreqstatus_002.html:Wed, 27 Jun 2018 08:29:42 GMT /sys/printreqstatus_003.html:Thu, 28 Jun 2018 15:03:49 GMT /sys/printreqstatus_004.html:Sun, 01 Jul 2018 13:04:20 GMT /sys/printreqstatus_005.html:Sun, 01 Jul 2018 13:30:15 GMT /sys/printreqstatus_006.html:Sun, 01 Jul 2018 14:10:48 GMT /sys/printreqstatus_007.html:Tue, 03 Jul 2018 09:13:32 GMT /dat/:Sun, 24 Jun 2018 18:35:43 GMT /dat/breachlog.html:Tue, 03 Jul 2018 09:14:27 GMT
| This page is a work in progress and will be updated as new developments emerge. If you have information you think should be added, please create an account to enable page edits or contact a Wiki Editor. |